Dark Web Profile: Andariel
Dark Web Profile: Andariel
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
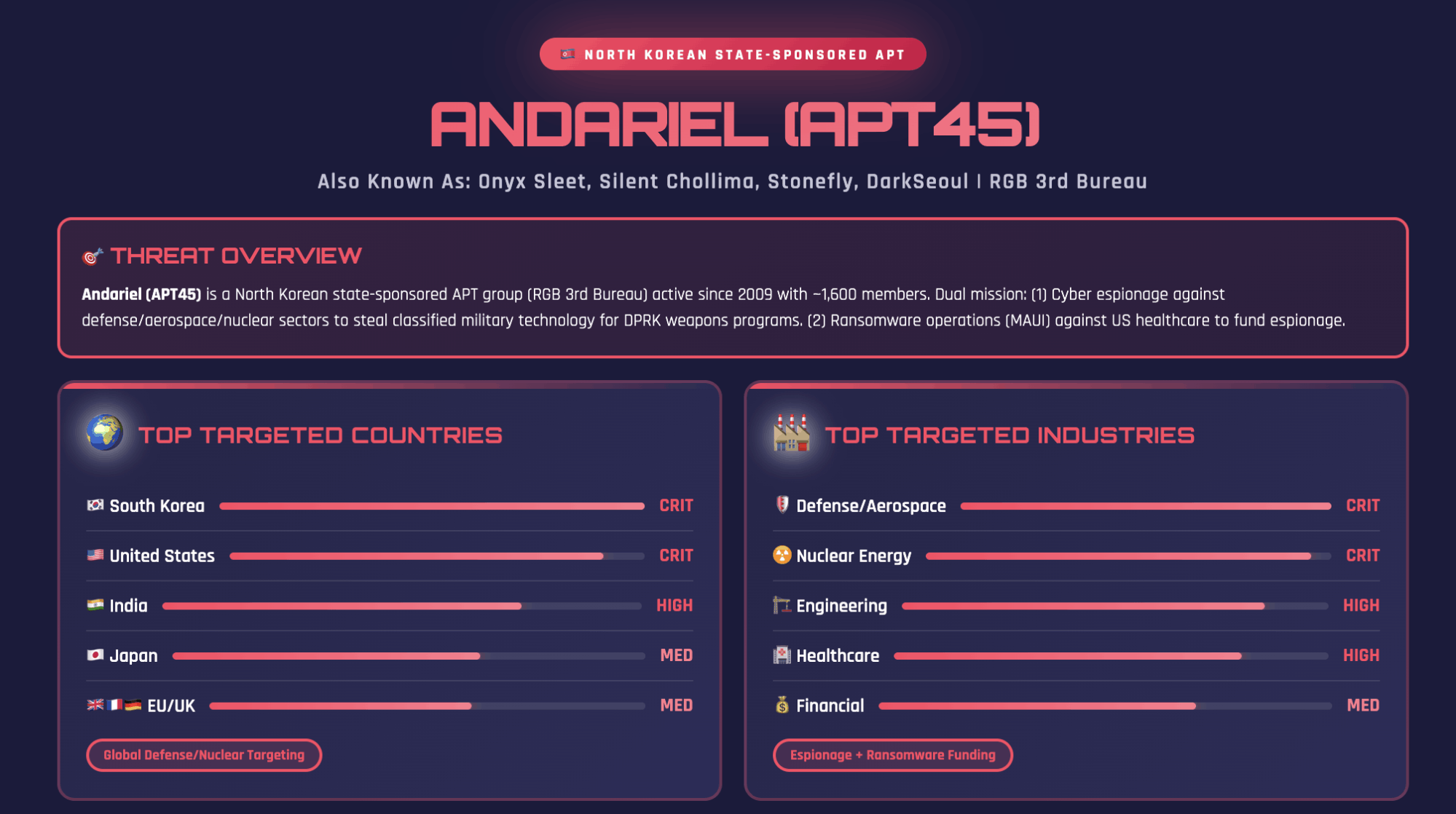
Andariel operates as a North Korea–linked threat group under the Reconnaissance General Bureau (RGB). Security researchers widely assess it as a sub-cluster of the Lazarus Group. Since around 2009, Andariel has moved from regional disruption campaigns to global cyber-espionage and revenue-driven operations.
The group targets defense contractors, nuclear engineering firms, financial institutions, healthcare providers, and software vendors. It blends intelligence collection with ransomware activity and cryptocurrency theft. This hybrid model reflects the DPRK’s strategy of using cyber operations both for strategic intelligence and hard currency generation.
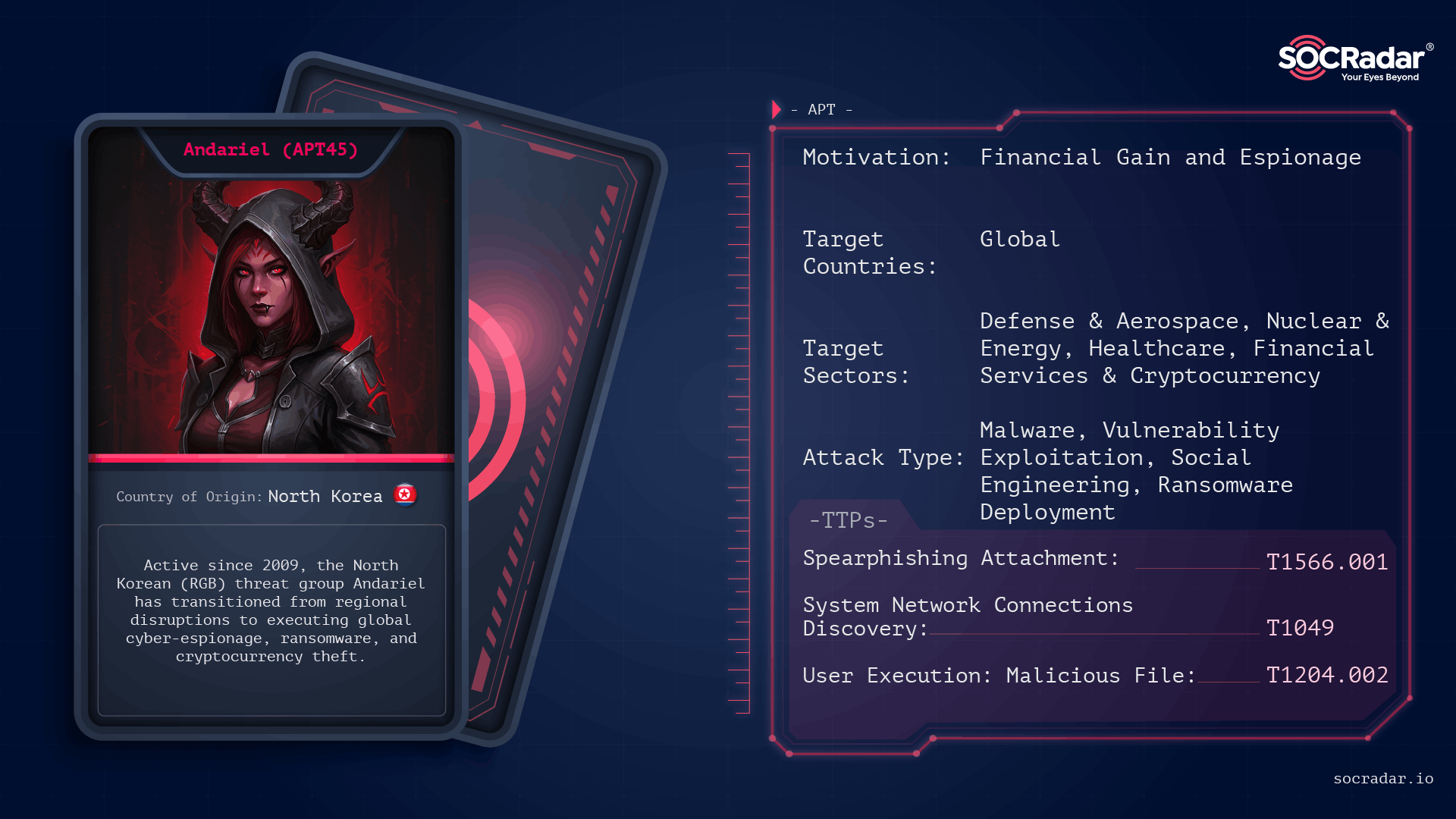
Threat Actor card of Andariel
Who is Andariel?
Andariel functions as an operational unit within North Korea’s Reconnaissance General Bureau. Public reporting links it to the RGB’s 3rd Bureau, also known as Bureau 121 or Lab 110. Some sources reference the internal designation 414 Liaison Office, indicating a structured role inside the military intelligence apparatus.
North Korea runs a centralized but flexible cyber structure. Multiple clusters operate under the Lazarus umbrella. They share tooling, infrastructure, and sometimes personnel. This overlap complicates attribution, but Andariel maintains a consistent operational profile that distinguishes it from other DPRK-linked groups.
Researchers track Andariel under several aliases, including Onyx Sleet, Silent Chollima, Dark Seoul, Stonefly, Plutonium, APT45, and Wassonite. These names reflect different vendor classifications, not separate entities.
| Threat Actor Alias | Tracking Organization | Assessment Confidence | Primary Sector Focus |
| Andariel | US Government/FBI | High | Defense, Nuclear, Aerospace |
| Onyx Sleet | Microsoft | High | IT Services, Energy, Defense |
| APT45 | Mandiant/Google | High | Critical Infrastructure, Healthcare |
| Silent Chollima | CrowdStrike | High | Government, Finance, Defense |
| Stonefly | Symantec/Broadcom | Moderate | Nuclear, Engineering |
| Jumpy Pisces | Palo Alto Unit 42 | High | Ransomware, Espionage |
Andariel maintains close operational alignment with BlueNoroff (APT38) and other Lazarus-linked clusters. It reuses code, adapts shared malware frameworks, and shifts focus based on regime priorities. When strategic objectives demand espionage, it targets defense and aerospace sectors. When financial pressure increases, it pivots toward ransomware and crypto theft.
The threat group operationalized ransomware as a state revenue tool. Rather than acting as a typical cybercriminal ransomware affiliate, Andariel deployed strains such as Maui and later SHATTEREDGLASS against healthcare providers, energy companies, and other critical infrastructure targets.
In practice, Andariel does not operate as an isolated hacking team. It functions as a structured component of North Korea’s state-directed cyber apparatus, integrating espionage, disruption, and financial operations under centralized command authority.
What Are Andariel’s Targets?
Andariel primarily targets organizations that align with North Korea’s military and financial priorities. South Korea remains the group’s main focus, but it also conducts sustained operations against the United States, Japan, several European countries, and parts of Southeast and South Asia. In the U.S. and Europe, Andariel has targeted defense contractors, aerospace firms, healthcare providers, and legal sector entities. In South Korea and Japan, it concentrates on defense manufacturers, telecommunications providers, semiconductor firms, and engineering companies. More recent activity shows increased interest in ERP vendors and software supply chains to gain indirect access to multiple downstream victims.
Andariel Threat Intelligence Report (Source: SOCRadar MCP)
Sector-wise, Andariel prioritizes defense and aerospace programs linked to missile systems, radar technologies, UAV development, and satellite components. It also targets nuclear and energy-related organizations for strategic intelligence collection. In parallel, the group conducts ransomware campaigns against healthcare and critical infrastructure entities and pursues direct theft from financial institutions and cryptocurrency platforms. This dual model allows Andariel to extract military intelligence while generating foreign currency to sustain future operations.
How Does Andariel Execute Its Operations from Initial Access to Exfiltration and Ransomware Deployment?
Andariel follows a structured intrusion lifecycle that combines opportunistic exploitation, credential-driven lateral movement, intelligence collection, and in some cases, ransomware deployment. The group’s operations are disciplined rather than noisy, progressing in controlled stages.
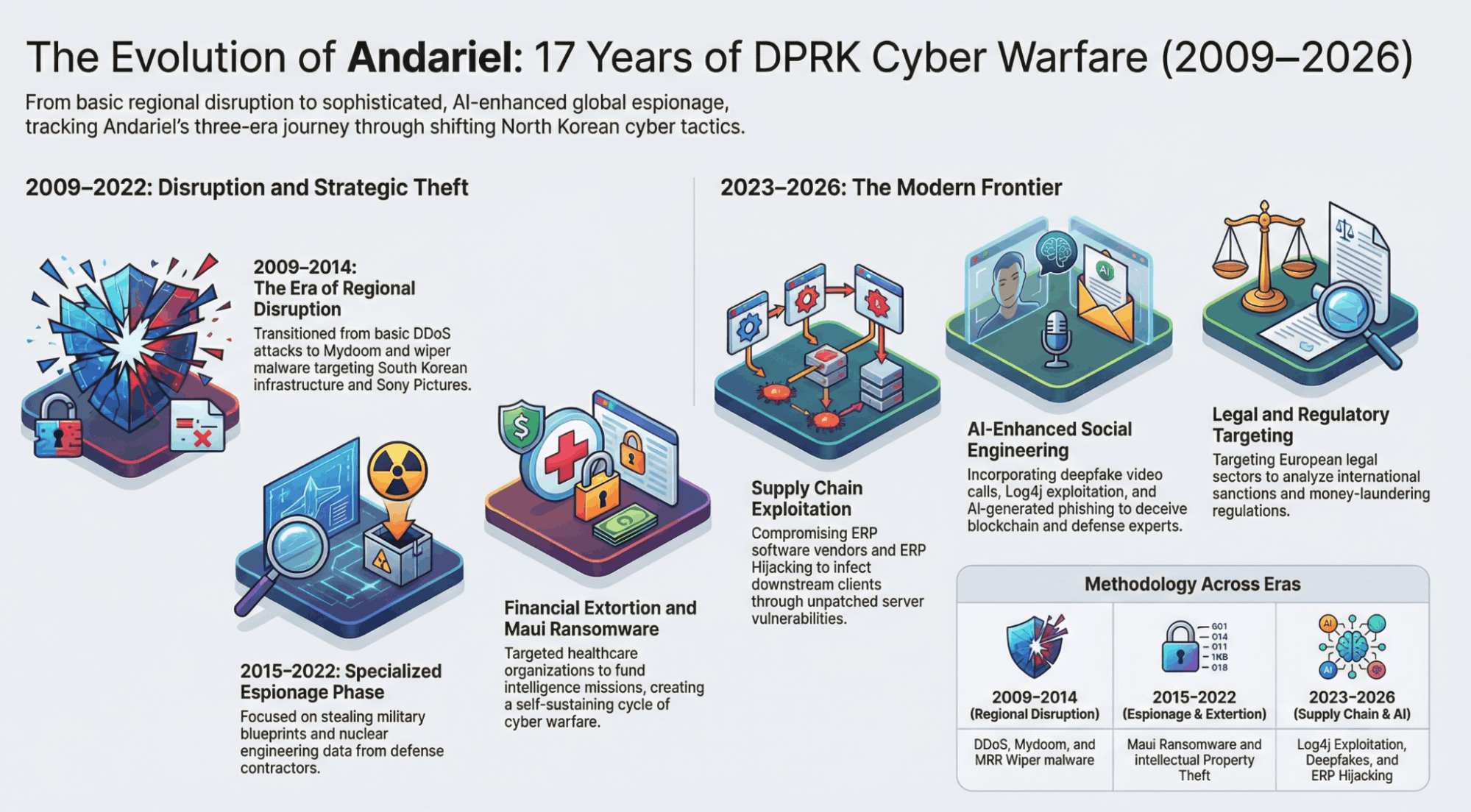
The Evolution of Andariel
Initial Access Vectors
The group frequently targets unpatched, internet-facing systems.
- Vulnerability exploitation: Andariel has leveraged N-day flaws, including CVE-2021-44228 (Log4Shell) affecting VMware Horizon, as well as vulnerabilities in Apache Tomcat and on-premises Microsoft SharePoint servers.
- Spear-Phishing and Social Engineering: While the shift toward vulnerability exploitation is evident, Andariel continues to utilize spear-phishing as a primary entry vector, often with themes tailored to the target’s professional interests. The group has been known to use job-seeking lures, impersonating recruiters or reputable organizations to deliver malicious attachments. These attachments often take the form of encrypted or unencrypted ZIP archives containing Microsoft Windows Shortcut (LNK) files or HTML Application (HTA) scripts.
- Watering hole attacks: Websites regularly visited by targeted sectors are compromised to distribute malware to visitors.
Lateral Movement and Credential Access
Once inside, credential access becomes the operational priority.
- Living-off-the-Land (LotL): Native Windows utilities such as PowerShell, WMI, and command-line tools are abused to reduce detection risk.
- Credential dumping: Tools like Mimikatz, ProcDump, and NirSoft’s CredentialsFileView are used to extract credentials from LSASS memory and registry stores.
- RDP and SSH abuse: Harvested credentials enable access to additional systems through RDP, SSH, and SMB, allowing movement toward sensitive servers and administrative infrastructure.
Data Staging, Exfiltration, and Ransomware Impact
Collected data is typically staged locally, compressed, and transferred to attacker-controlled infrastructure. In financially motivated operations, this phase may transition into ransomware deployment.
- Cloud storage misuse: Operators have logged into cloud storage services such as MEGA directly from compromised networks, uploading data with tools like WinSCP and PuTTY.
- C2 tunneling: Utilities such as 3Proxy, PLINK, and Stunnel tunnel command-and-control traffic over legitimate protocols, masking data transfer activity.
- Ransomware execution: In certain campaigns, once data theft is complete, Andariel deploys ransomware to encrypt systems and increase leverage. This dual-purpose approach blends espionage tradecraft with financial extortion, expanding operational impact.
The sequence is consistent: exploit exposed systems, obtain credentials, move laterally with minimal noise, stage and exfiltrate data, and, where aligned with objectives, apply ransomware pressure. The effectiveness lies not in exotic tooling but in disciplined execution and adaptive targeting.
version strings before switching to encrypted TCP command channels.
Key Malware Families
- Maui: Manually executed ransomware using AES-128 per file, RSA-protected keys (maui.key / maui.evd), and XOR obfuscation derived from disk identifiers. Generates maui.log for operator-side decryption workflows.
- DTrack: Lazarus-linked backdoor supporting file transfer, keylogging, screenshots, and lateral movement. Newer variants employ process hollowing (e.g., explorer.exe).
- TigerRAT: C++ RAT with file control, command execution, SOCKS tunneling, and encrypted HTTP-like communications. Used in defense-sector intrusions.
- EarlyRat: Lightweight HTTP-based malware delivered via Log4j exploitation or phishing, using Base64 and rolling XOR in C2 parameters.
- Atharvan: Custom RAT creating a mutex (SAPTARISHI-ATHARVAN-101) and disguising C2 traffic as legitimate Microsoft update traffic.
Additional campaigns feature Dora RAT (DLL side-loading via WinRAR SFX), DurianBeacon (Go/Rust variants), and NukeSped lineage malware with registry-based configuration storage.
How Can Organizations Mitigate the Andariel Attack Chain?
To counter the Andariel attack chain, organizations should apply a layered security model that disrupts activity at each stage of intrusion:
- Vulnerability and patch management: Rapidly remediate critical vulnerabilities in CI/CD pipelines, web applications, and remote access systems. Focus on externally exposed assets and high-privilege services.
- Identity and access management: Enforce MFA across all user and administrative accounts. Audit for suspicious account creation, especially accounts designed to resemble legitimate system identities such as KRBTGT.
- Network segmentation: Separate critical infrastructure and sensitive data repositories from standard user environments. Limit east-west movement through strict access controls and firewall policies.
- Endpoint security: Deploy EDR tools capable of detecting LSASS memory access, custom tunneling or proxy utilities, and the abuse of vulnerable signed drivers (BYOVD techniques).
- Protocol monitoring: Monitor internal RDP and SMB traffic for anomalous patterns. Restrict administrative shares and apply least-privilege access principles.
- Backup and recovery: Maintain immutable, offline backups to ensure operational resilience against ransomware deployment.
Threat intelligence integration and proactive threat hunting remain critical. As Andariel evolves from a regionally focused actor into a broader ransomware and espionage operator, coordinated and technically disciplined defensive strategies are necessary to detect, contain, and disrupt its campaigns at scale.
What Are the MITRE ATT&CK TTPs of Andariel?
| Tactics | ID | Name | |
| Collection | T1005 | Data from Local System | |
| Initial Access | T1189 | Drive-by Compromise | |
| Execution | T1203 | Exploitation for Client Execution | |
| Reconnaissance | T1592 | .002 | Gather Victim Host Information: Software |
| Reconnaissance | T1590 | .005 | Gather Victim Network Information: IP Addresses |
| Command and Control | T1105 | Ingress Tool Transfer | |
| Defense Evasion | T1027 | .003 | Obfuscated Files or Information: Steganography |
| Resource Development | T1588 | .001 | Obtain Capabilities: Malware |
| Initial Access | T1566 | .001 | Phishing: Spearphishing Attachment |
| Discovery | T1057 | Process Discovery | |
| Discovery | T1049 | System Network Connections Discovery | |
| Execution | T1204 | .002 | User Execution: Malicious File |
Article Link: https://socradar.io/blog/dark-web-profile-andariel/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics