Adversary Consolidation: Per-Host Attack Intensity Doubles in February 2026
The cybersecurity threat landscape in February 2026 revealed a significant strategic shift in adversary behavior. While raw event volume experienced a minor decline, the infrastructure supporting these attacks underwent a massive consolidation. This report distills nearly 200 million event data points from the HoneyDB global sensor network to identify emerging patterns in automated exploitation. For security operations teams, the data suggests a move away from broad, low-intensity scanning toward more aggressive, high-frequency engagement from a smaller pool of compromised hosts.
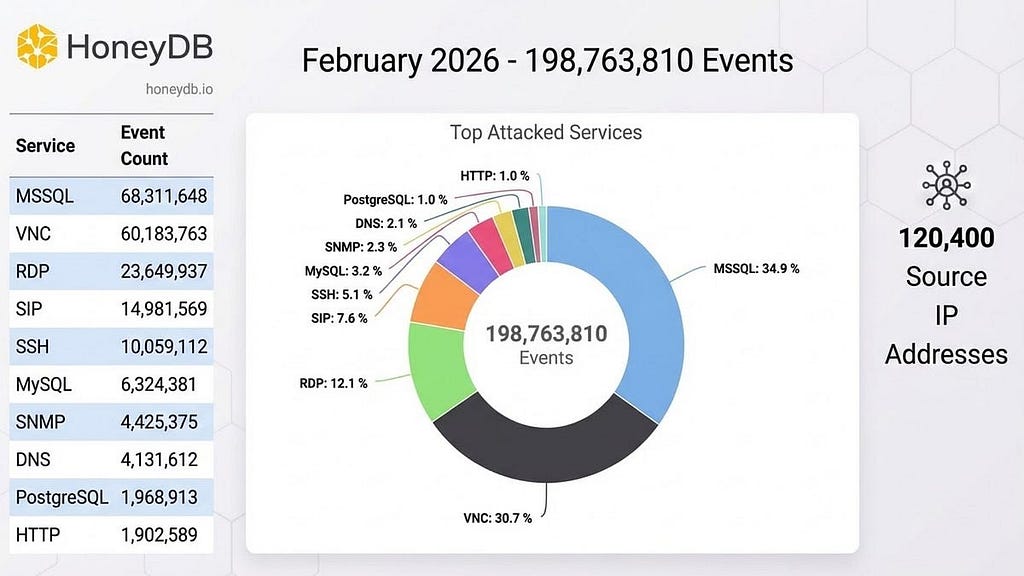
February 2026 by the Numbers
February’s telemetry captured a high concentration of activity across a select group of protocols. The primary metrics for the period are as follows:
- Total Events: 198,763,810
- Total Unique Remote Hosts: 120,400
Top Five Targeted Services:
- MSSQL (Port 1433): 68,311,648 events
- VNC (Port 5900): 60,183,763 events
- RDP (Port 3389): 23,649,937 events
- SIP (Port 5060): 14,981,569 events
- SSH (Port 22): 10,059,112 events
Analysis of Attack Distribution: January vs. February
Comparing February’s data to the preceding month reveals a significant contraction of active adversary infrastructure. In January 2026, the network recorded 218,177,148 events originating from 248,608 unique remote hosts. In February, while total event volume dropped by approximately 9% to 198,763,810, the count of unique remote hosts plummeted to 120,400.
This represents a more than 50% reduction in the number of unique systems participating in global scanning. However, the “so what” for threat intelligence leads is found in the per-host intensity: in January, the average number of events per host was approximately 877. In February, that figure surged to approximately 1,650. Adversaries are not slowing down; they are simply driving their remaining infrastructure twice as hard.
Protocol-Specific Trends and Strategic Shifts
Concentration of Force The near-doubling of per-host attack intensity implies a more efficient use of command-and-control (C2) infrastructure. Instead of maintaining a vast, distributed network of low-reputation bots-which are easily flagged and blocked-threat actors appear to be utilizing a smaller group of higher-quality, perhaps more stable, compromised hosts to maintain persistent pressure on targets.
The VNC Surge and Database Pivot One of the most dramatic shifts occurred in the targeting of remote access tools. Virtual Network Computing (VNC) attacks nearly doubled, jumping from 30.5M in January to over 60.1M in February. This surge coincided with a sharp decline in MSSQL targeting, which dropped from 113.1M to 68.3M. This suggests a strategic pivot; as database environments harden or become less profitable for automated exploitation, adversaries are refocusing their high-intensity resources on direct remote-access vulnerabilities.
DNS as an Outlier Domain Name System (DNS) activity emerged as a significant technical outlier. DNS events rose from 1.6M in January to over 4.1M in February. This 150% increase is notable because DNS has now surpassed MySQL, PostgreSQL, and HTTP in total volume. This growth likely signals an increase in reconnaissance tactics or the preparation of infrastructure for DNS amplification attacks, marking it as a protocol to monitor closely in the coming quarter.
Technical Hypothesis and Outlook
The transition to a model of “efficiency over volume” likely reflects an evolution in botnet management. This consolidation may be a defensive reaction to improved automated filtering: by concentrating attacks through fewer hosts, adversaries can better manage the reputation of their exit nodes and increase the frequency of hits before a host is blacklisted.
As we move into the spring of 2026, we expect this trend of high-intensity, targeted scanning to continue. The central question for defenders is whether this consolidation indicates a refinement of automated infrastructure for better C2 efficiency, or if we are seeing the emergence of more resilient, “high-reputation” botnets designed to bypass traditional IP-based reputation scoring.
Query the Dataset
To perform your own analysis on these trends or integrate this intelligence into your security stack, we invite you to leverage the HoneyDB ecosystem.
- API Integration: Sign up at honeydb.io to access real-time threat data.
- Sensor Contribution: Contribute to global threat visibility by deploying a honeypot and sharing telemetry with the community.
Originally published at https://deception.substack.com.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics
