Alleged FNATH, AT&T, Rapikom, Canva, and Canada Data Listings Plus Windows Bot Rental
Alleged FNATH, AT&T, Rapikom, Canva, and Canada Data Listings Plus Windows Bot Rental
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
SOCRadar’s Dark Web Team identified several new underground posts this week, including alleged database sales tied to FNATH and AT&T, a claimed free leak involving Rapikom Venezuela, and credential-focused listings referencing Canva and Canadian “leads” data. Another post advertised a Windows bot offered as a rental service, with claims of browser and wallet theft, remote access, and AV/EDR evasion features.
Receive a Free Dark Web Report for Your Organization:
The Alleged Leads Data of Canadian Citizens are on Sale

SOCRadar Dark Web Team detected a threat actor post on a dark web forum advertising the sale of an alleged 6.5 million-record “leads” dataset associated with Canadian citizens.
According to the post, the data was claimed to be collected from advertising campaigns and listed fields such as client names, phone numbers, mobile numbers, email addresses, and country values. The seller priced the dataset at $3,500 and stated they were selling data only, not access.
Alleged User Accounts of Canva are Leaked
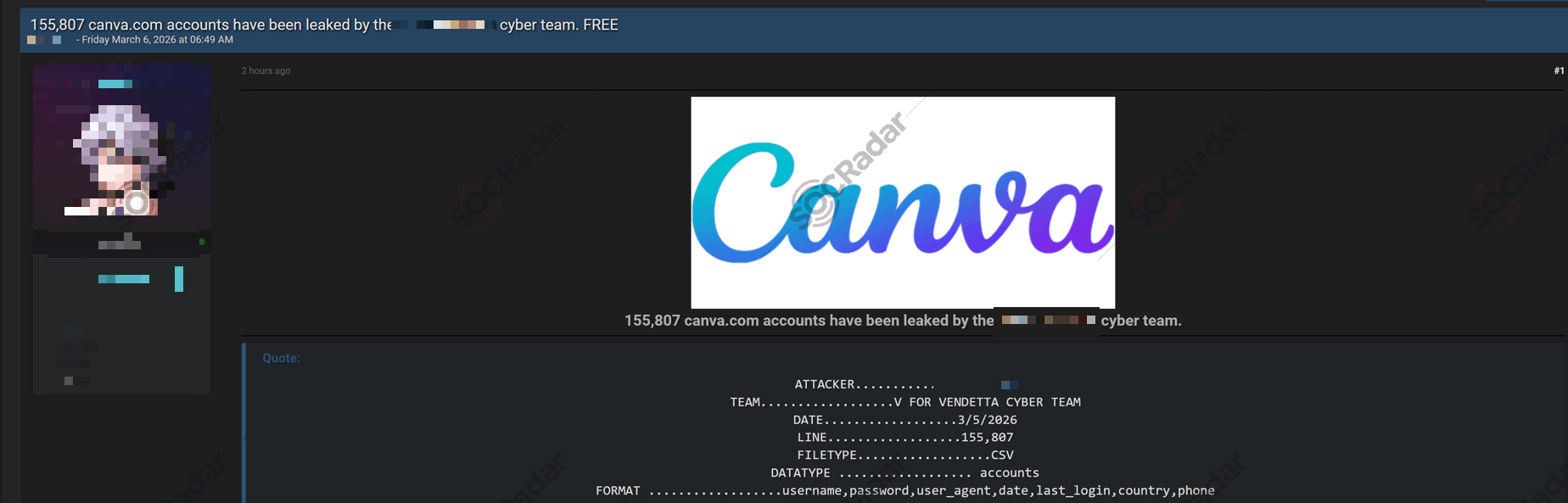
SOCRadar Dark Web Team detected a threat actor post on a dark web forum claiming the leak of 155,807 Canva.com accounts, attributed in the post to a group labeled V for Vendetta Cyber Team.
According to the post, the dataset was described as a CSV and the listed format included username, password, user_agent, date, last_login, country, and phone fields. The post also included a dated header and a short “quote-style” block summarizing the claimed dataset structure.
The Alleged Database of Rapikom is Leaked

SOCRadar Dark Web Team detected a threat actor post on a dark web forum claiming a free database leak linked to RAPIKOM VENEZUELA, described as a platform with affiliates and company-related records.
The listing claims the dataset contains records tied to 5,000 companies and includes business fields such as contact details, plan information, purchase and payment references, and a password field labeled usr_clave. According to the threat actor, the dataset also contains bank account information and precise location data (latitude and longitude) for each company.
The Alleged Database of FNATH is on Sale
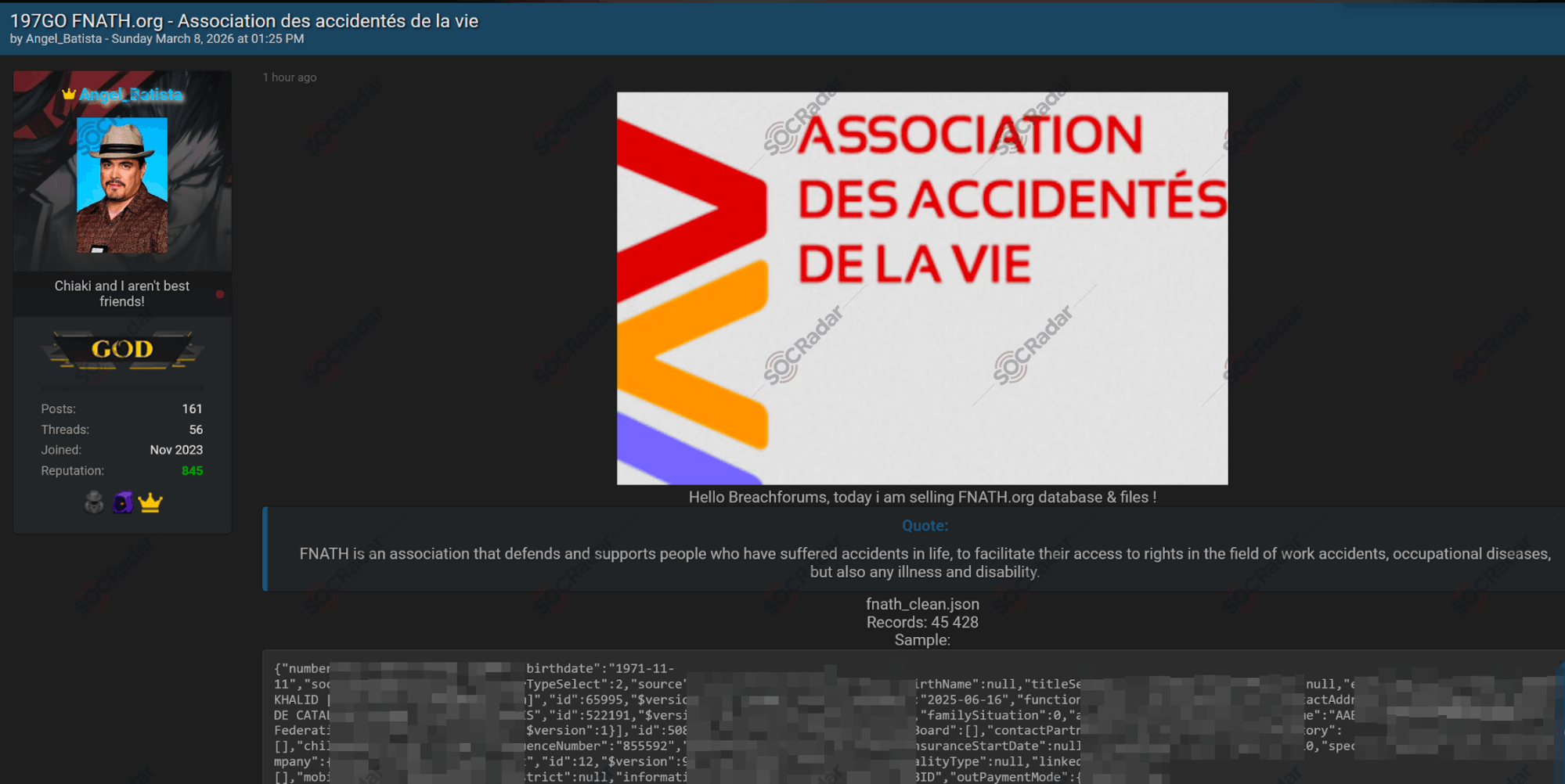
SOCRadar Dark Web Team detected a threat actor post on a dark web forum advertising the sale of an alleged database and files linked to FNATH.org, an association that supports individuals affected by accidents, occupational disease, illness, and disability.
According to the post, the actor referenced a database file labeled fnath_clean.json with 45,428 records and shared partial samples. The listing also claimed access to “case files” and referenced a large archive size of 197GB, implying broader document exposure beyond basic membership records.
The Alleged Database of AT&T is on Sale
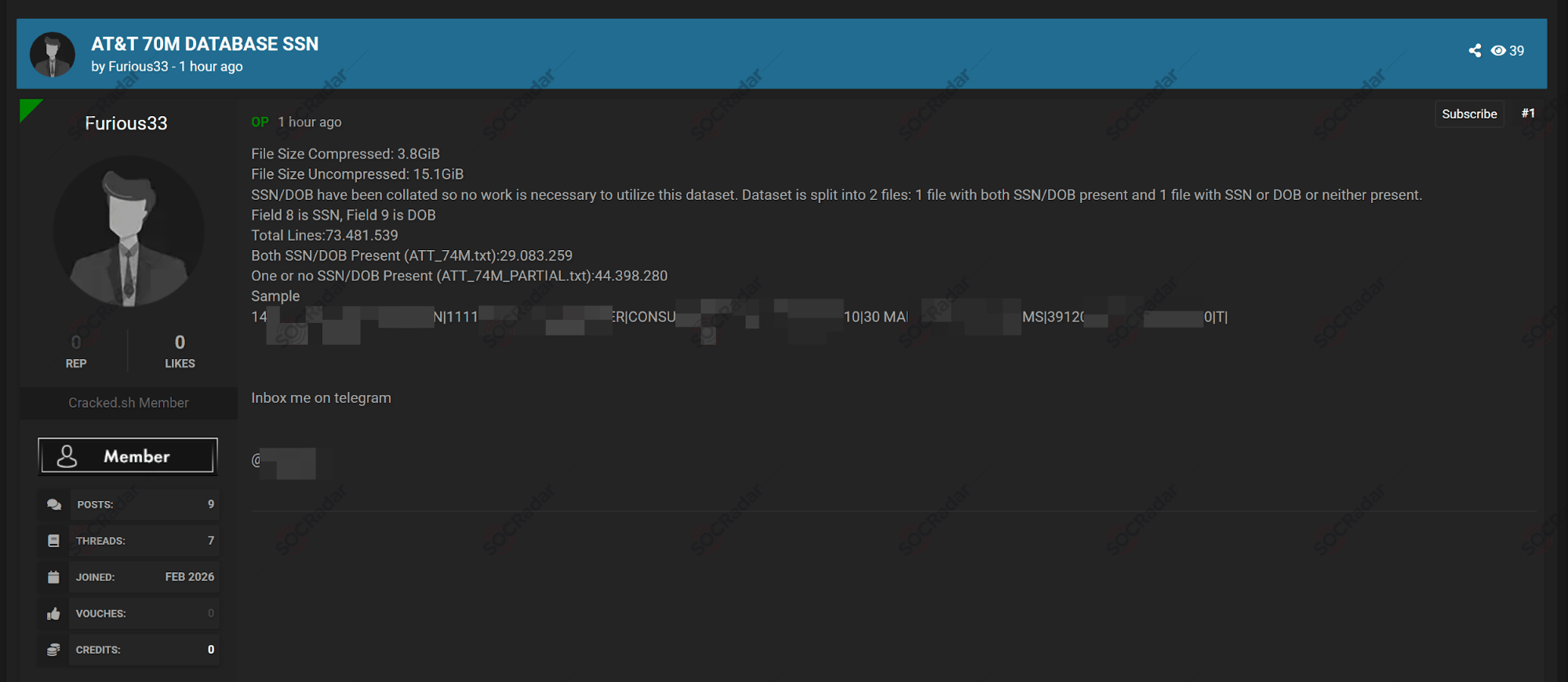
SOCRadar Dark Web Team detected a threat actor post on a dark web forum advertising an alleged AT&T dataset described as containing 73,481,539 lines.
According to the post, the dataset was presented as split into two files and marketed as “collated” for use, with the seller explicitly referencing SSN and DOB fields. The listing claimed 29,083,259 lines contained both SSN and DOB, while 44,398,280 lines contained one or neither. File size details were also included, along with a short sample line and Telegram contact instructions.
New Windows Bot Rental is Detected
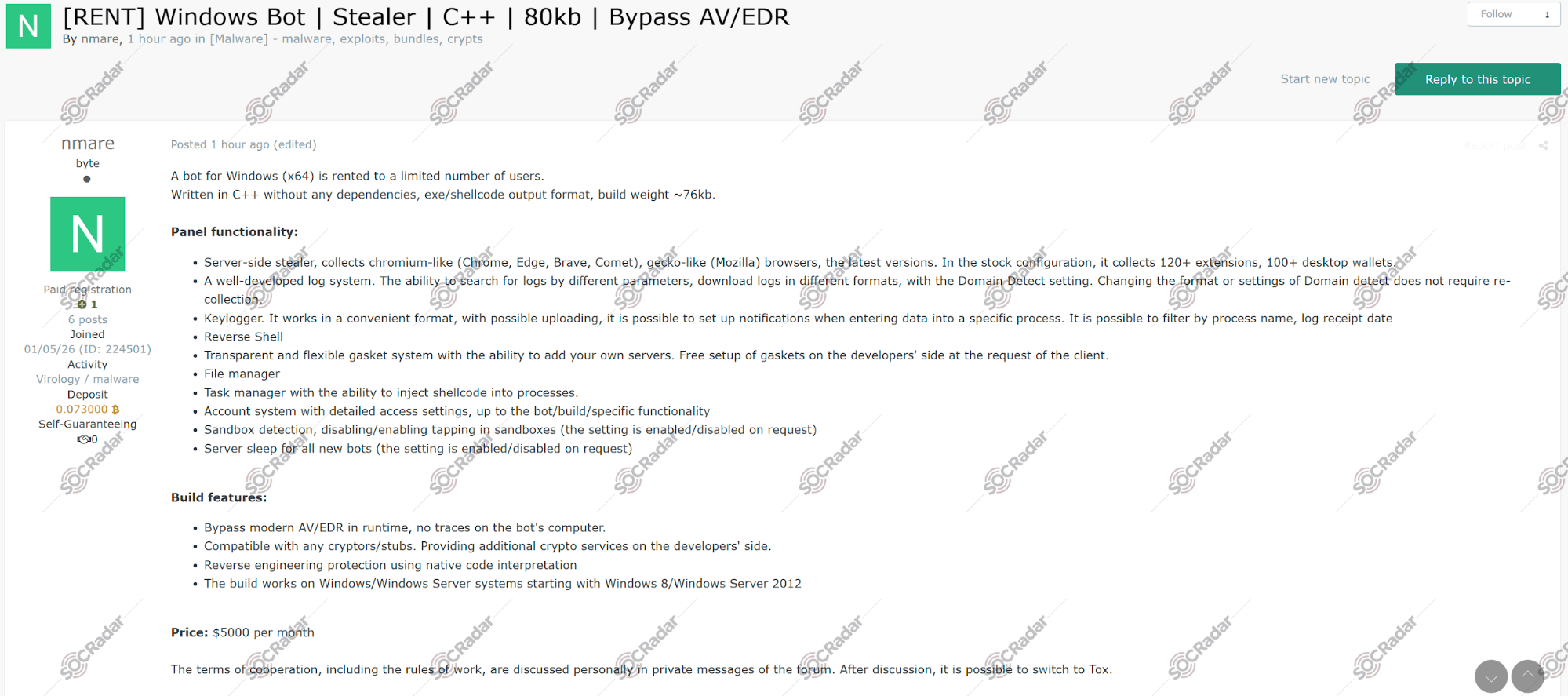
SOCRadar Dark Web Team detected a threat actor post on a dark web forum advertising a Windows bot offered for rent, described as a C++ build for Windows x64 with a small footprint and multiple control features.
In the advertisement, the actor claims the bot supports browser data theft from Chromium-based and Mozilla browsers, collection of extensions, theft targeting desktop crypto wallets, and a logging panel with search and export functions. The post also lists capabilities including a keylogger, reverse shell, file management, task injection, sandbox checks, and runtime AV/EDR bypass features. The price is listed as $5,000 per month, with private negotiation and optional Tox contact.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.
Article Link: https://socradar.io/blog/fnath-att-rapikom-canva-and-canada-data/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics

