Police Force Challenges 2026

Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Crime in 2026 is younger, faster, more decentralized and more data-driven than at any point in modern policing history. Criminal activity increasingly unfolds across digital platforms, encrypted channels, borderless financial systems and transnational networks that move at the speed of technology rather than bureaucracy.
Law enforcement agencies face simultaneous pressure from changing offender and victim demographics, increasing illicit border activity and cybercrime. At the same time, the scale of digital activity in our modern world generates an overwhelming volume of data that must be turned into decisions under real-world time constraints. Traditional investigative models built around siloed tools and manual workflows are struggling to keep pace.
Success in this environment increasingly depends on enabling investigators and analysts to fuse data across domains, surface meaningful context and generate timely, actionable intelligence rather than isolated pieces of evidence.
This blog examines the external and internal challenges shaping law enforcement operations in 2026 and the technology capabilities required to address them.
External Challenges
Changing Offender and Victim Dynamics
Crime is increasingly shaped by digital native behavior. Younger generations live in online-first environments where identity, communication, financial activity and social interaction are tightly intertwined. Criminal activity exploits these behaviors, often blending seamlessly into everyday digital life rather than appearing as overt criminal acts.
Gen Z and Gen Alpha frequently surface in investigations as facilitators, money mules and recruits, sometimes without fully understanding their role in a criminal network. At the same time, they are highly exposed as victims of grooming, fraud, sextortion and digital harassment. Many of these activities occur in group chats, gaming platforms, peer-to-peer payment apps and social ecosystems where traditional policing has limited visibility.
Public perception of crime and trust in law enforcement are also increasingly shaped online. Narratives, misinformation and viral content can influence community response long before official information is released.
Law enforcement intelligence reporting indicates that minors are now involved in more than 70% of criminal markets in Europe, often tasked with roles ranging from cash couriers to violent activities including extortion and murder.
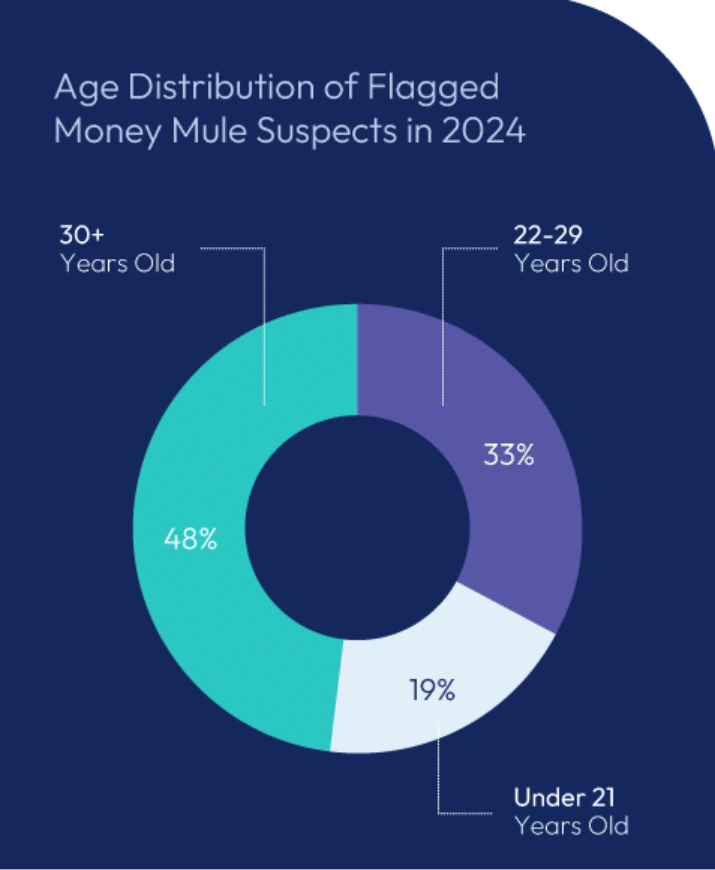
For example, the UK financial regulatory body Financial Conduct Authority reports shows that in 2024 over 207,889 personal accounts were flagged as money mules, with one-third of suspects aged 22–29, as recruiters leveraged social media ‘opportunity’ ads to enlist unwitting participants into laundering schemes. Although the fraud prevention service Cifas estimates that at least 19% of known money mules are under 21, the true figure is likely higher because no data is recorded for those under 16.
Early Detection of Digital Crimes with OSINT
OSINT capabilities are essential for identifying early indicators of digitally native crime. Law enforcement agencies must be able to gather and analyze open-source data at scale across social platforms, forums, messaging spillover, gaming-adjacent communities and emerging online ecosystems. This goes beyond traditional social media visibility. A wide OSINT approach enables agencies to detect recruitment efforts, grooming behavior, emerging fraud narratives and coordinated activity before it escalates into real-world harm.
Blockchain intelligence is increasingly critical as younger generations normalize cryptocurrency use for everyday transactions. Many Gen Z and Gen Alpha related investigations involve crypto wallets, in-game currencies, NFTs and peer-to-peer payment mechanisms. Blockchain intelligence allows investigators to trace illicit financial flows and link criminals directly to their crypto wallets, even when criminals attempt to obscure activity through mixers or decentralized platforms.
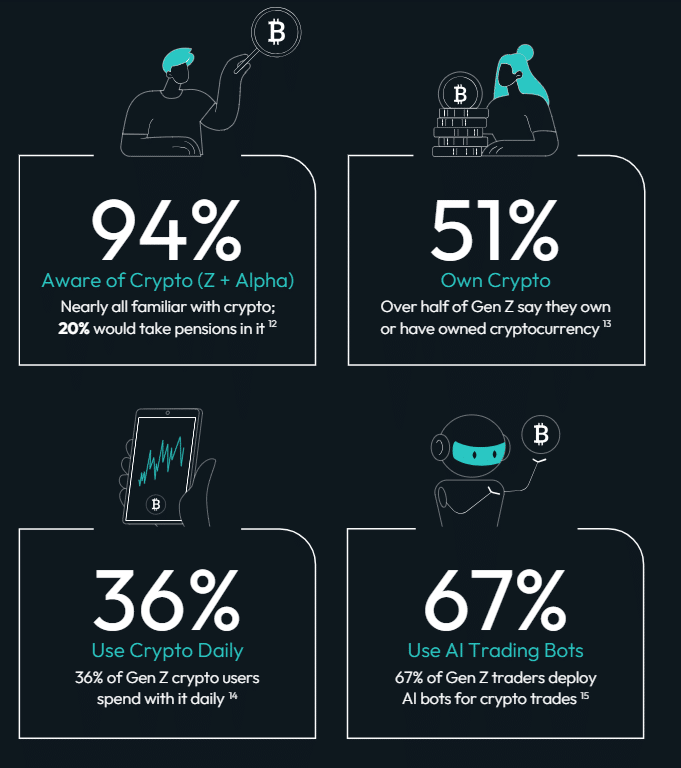 Digital habits of Gen Z, Cognyte’s Crime Goes Digital Native report 2026
Digital habits of Gen Z, Cognyte’s Crime Goes Digital Native report 2026 Increasing Cross-Border Crime
Cross-border crime now operates at industrial scale. Criminal networks function like global enterprises, with logistics chains, financial operations, recruitment pipelines and communications infrastructure spread across multiple jurisdictions. These networks deliberately exploit gaps between national authorities, regulatory regimes and enforcement mandates. It’s not just about sharing information but a lack of communication between agencies that criminals exploit.
Borders themselves have evolved. Crime flows through ports, land crossings, maritime routes and airspace, but also through digital infrastructure, satellite connectivity and financial systems that ignore geography. Smuggling, trafficking, sanctions evasion and illicit trade increasingly rely on technology to move faster than traditional border controls.
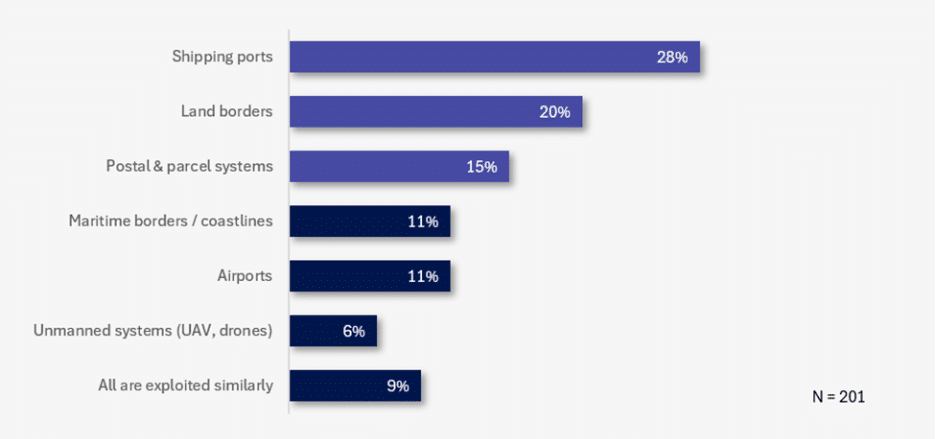 Most Exploited Entry Point for Cross-Border Crimes in Jurisdiction (Last 2 Years), Cognyte’s European Law Enforcement Agencies Survey 2026
Most Exploited Entry Point for Cross-Border Crimes in Jurisdiction (Last 2 Years), Cognyte’s European Law Enforcement Agencies Survey 2026 INTERPOL estimates that transnational organized crime generates over $1 trillion annually, exploiting gaps in national laws, enforcement capacity and border controls.
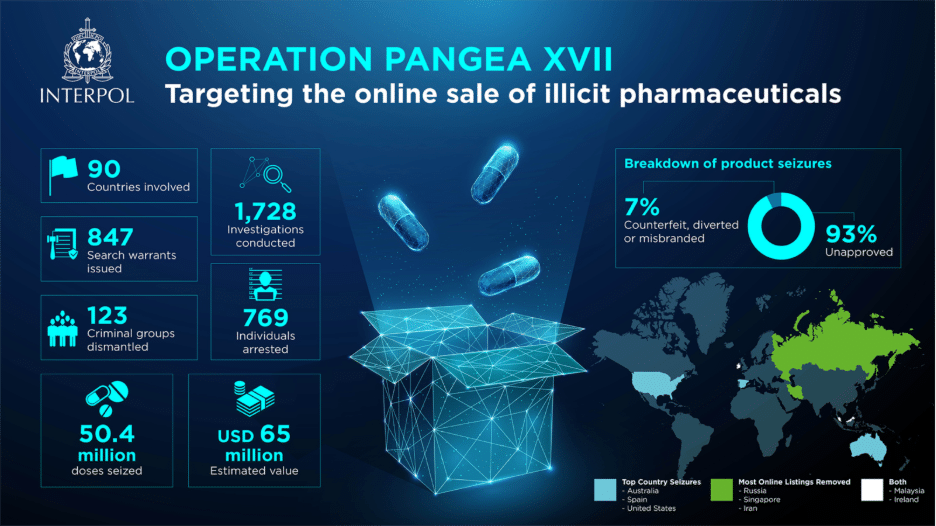
Criminal gangs routinely exploit complex supply chains moving counterfeit pharmaceuticals through multiple intermediaries, repackagers and distribution networks before detection. In 2025 an INTERPOL-coordinated operation across 90 countries resulted in the seizure of 50.4 million doses of illicit pharmaceuticals worth USD 65 million, highlighting the alarming scale of the global trade in unapproved and counterfeit medicines.
How to Address the Challenge of Cross-Border Crime
Border intelligence enables agencies to move from reactive interdiction to proactive disruption. By fusing maritime, land, air, cyber and open-source data, border intelligence provides a holistic operational picture of cross-border activity. This allows agencies to identify smuggling corridors and prioritize high-risk routes. This helps distinguish between humanitarian movement and criminal exploitation, resulting in effective allocation of limited resources across jurisdictions.
Blockchain intelligence plays a critical role in exposing the financial backbone of cross-border crime. Smuggling networks increasingly rely on cryptocurrency to move funds, pay facilitators and launder proceeds across borders with minimal friction. Blockchain intelligence allows investigators to trace payments and identify network nodes. This connects financial activity to logistics operations, supporting coordinated enforcement across customs, border protection and law enforcement agencies.
Increasing Cybercrime and Online Scams
Cybercrime and online scams continue to grow in volume and sophistication, accelerated by the widespread use of generative AI. Criminals can now rapidly create convincing phishing messages, deepfake audio or video, impersonation campaigns and personalized fraud narratives that are difficult for victims to distinguish from legitimate communications.
These crimes are no longer isolated or opportunistic. Romance scams, investment fraud, ransomware and extortion are often run as coordinated operations with shared infrastructure, shared tooling and defined roles across multiple actors. Digital platforms allow these networks to scale quickly while remaining geographically dispersed.

According to the 2024 FBI Internet Crime Report, US law enforcement received over 859,000 complaints of suspected internet crime with reported losses exceeding $16 billion, a 33% increase from the year before and investment scams alone caused more than $6.5 billion in losses. This surge demonstrates how cyber-enabled fraud now operates at industrial scale, outpacing many traditional investigative responses.
A widely reported individual case featured a 75-year-old U.S. retiree who lost more than $715,000 of his life savings to a pig-butchering scam that began with a LinkedIn message from a fraudulent persona. Over several months of WhatsApp communication, the scammer cultivated a relationship, then guided him into repeated “investments” on a fake trading platform, ultimately draining his accounts and leaving him with no funds to recover.
How to Address the Challenge of CyberCrime
Decision intelligence solutions are essential for turning fragmented cyber indicators into actionable investigations. These law enforcement solutions fuse cyber telemetry, communications data, financial transactions, OSINT and investigative records into a single analytical environment. This allows analysts to identify patterns across incidents, link repeat offenders, prioritize threats and move faster from detection to disruption.
External threat intelligence provides critical context around emerging tactics, infrastructure reuse and criminal collaboration. By integrating external threat intelligence feeds with investigative data, agencies gain visibility into how cybercrime groups operate, how campaigns evolve and where defensive or investigative action will have the greatest impact. This intelligence is particularly important when dealing with fast-moving AI-enabled scams that change tactics frequently.
Crime–Terror Convergence
The distinction between organized crime and terrorism is increasingly blurring. Criminal groups provide logistics, financing, forged documents, weapons and operational services to extremist organizations, while terror actors adopt criminal methods to fund activities and avoid detection.
This convergence complicates investigative responsibilities. Cases often span organized crime, counterterrorism, financial crime and border protection, requiring coordination across units that traditionally operated separately. Criminal and terror networks benefit from these seams, using them to hide relationships and obscure intent.
A systematic review of the “crime-terror nexus” found that about one-third of terrorist groups are involved in financial collaborations with organized crime, engaging in activities such as drug trafficking, money-laundering, and smuggling to sustain their operations.
In the UK, authorities have warned that both Russia and Iran are using criminals to carry out arson, sabotage and attacks on dissidents. MI5 Director General Ken McCallum disclosed that since January 2022, authorities had dealt with twenty Iranian-backed plots targeting UK citizens and residents, noting that “Iranian state actors make extensive use of criminals as proxies – from international drug traffickers to low-level crooks.
How to Address the Challenge
Decision intelligence platforms enable agencies to connect disparate data points across crime, terror and security domains. By correlating intelligence reports, financial data, communications, OSINT and operational records, decision intelligence platforms help investigators identify shared facilitators and overlapping logistics that would otherwise remain hidden in siloed systems.
Cross-agency intelligence sharing is critical in responding to converged threats. Crime–terror networks exploit gaps between local, state, federal and international organizations. Decision intelligence platforms enable information sharing and collaborative workflows allowing agencies to coordinate faster, align priorities and respond to complex threats that no single organization can address alone.
Internal Challenges
Manpower Shortages, Turnover and Information Overload
Many agencies face staffing shortages and high turnover, particularly among analysts and technical roles. At the same time, the volume of data tied to each investigation continues to grow. Digital forensics, OSINT, communications data, financial records, video and sensor feeds must all be reviewed, correlated and understood.
This creates a compounding problem. Experienced investigators are stretched thin, while newer staff often struggle with complex systems and unfamiliar data types. Valuable time is spent searching for information rather than analyzing it, increasing delays and investigative fatigue.

In England and Wales, the rate of positive crime outcomes, when suspects are identified and cases successfully concluded, fell from 25 % a decade ago to just 11 % in 2024, with investigators reporting that they often have only two days in every ten to work on ongoing investigations because they are constantly responding to new demands.
A precise illustration of this challenge comes from the Metropolitan Police in the UK, where detectives were pulled from a specialist cold case unit to support basic command operations, leaving historic murder inquiries such as the 1994 killing of Atek Hussain without dedicated investigative capacity and contributing to decades-long delays in case progression.
How to Address the Challenge
Intelligence co-pilots help investigators manage complexity by automating routine analytical tasks. These tools support natural-language querying, summarization, anomaly detection and lead prioritization.
In simple terms, natural-language querying allows an investigator to ask questions in plain language, such as “show me all connections between these two suspects in the last six months” or “which cases involve the same wallet address”. Instead of building complex database queries or navigating multiple systems, the system interprets the question and retrieves relevant results automatically.
Decision intelligence platforms provide the structural foundation for productivity. By unifying data sources and embedding analytics directly into investigative workflows, these platforms reduce duplication, shorten learning curves for new staff and ensure that insights are consistent and auditable across teams. This is especially critical in environments with frequent personnel turnover.
Limited Crypto and Financial Crime Expertise
Financial crime is no longer a specialized discipline. Cryptocurrency, shell companies, digital payments and complex ownership structures appear in a wide range of investigations, from fraud and cybercrime to trafficking and sanctions evasion.
Many agencies lack dedicated financial crime expertise, making it difficult to follow the money across digital and traditional systems. Without the ability to connect transactions, entities and funding mechanisms, financial networks often remain intact even when individual actors are identified.
The scale of crypto financial crime is substantial. In 2025, cryptocurrency holders globally lost an estimated $17 billion to scams and fraud, driven by impersonation tactics and AI-assisted schemes that outpaced traditional investigative and tracing capabilities.
A stark example of how complex financial crime can cross borders occurred in 2025 when Thai police, acting on intelligence from the Australian Federal Police, arrested 13 suspects operating a $1.2 million online investment scam that defrauded thousands of Australians through fake investment campaigns distributed via online ads and phone calls.
How to Address the Challenge
Wide OSINT is the systematic correlation and analysis of massive volumes of heterogeneous open-source data across many domains, platforms and geographies, to generate actionable intelligence at scale.
Wide OSINT integrated into decision intelligence allows agencies to contextualize financial activity. By combining blockchain data with commercial sources such as corporate registries, sanctions lists, adverse media and trade or shipping data, investigators can uncover beneficial ownership, identify shell companies and expose financial networks that support criminal operations.
Cognyte’s BLINK Reports Service helps law enforcement agencies quickly gain clarity in complex cryptocurrency and financial crime investigations. The service delivers analyst-ready reports that consolidate blockchain activity, wallet relationships and transaction patterns into a clear investigative view. Instead of spending time interpreting raw ledger data, investigators receive focused insights that identify suspicious flows, key entities and potential links to fraud, money laundering or sanctions evasion. This approach is particularly valuable when internal crypto expertise is limited or when time-sensitive intelligence is required, allowing teams to move investigations forward with greater speed and confidence.
Conclusion: Priorities for Law Enforcement Agencies in 2026
The challenges facing law enforcement in 2026 are interconnected. Generational change, borderless crime, digital acceleration and internal resource constraints reinforce one another.
Agencies that succeed will be those that:
- Detect early indicators of crime in digital-native environments
- Break the silos to see across borders and domains
- Counter AI-enabled crime with intelligence-driven decision-making
- Reduce investigator burden while improving speed, accuracy and accountability
Ultimately, the shift required is not simply technological. It is a shift enabling law enforcement agencies to move from reactive investigations to proactive, intelligence-led operations in a world where crime evolves faster than ever.
Today’s Criminal Threats Require An Intelligence-Powered Approach
The post Police Force Challenges 2026 appeared first on Cognyte.
Article Link: https://www.cognyte.com/blog/police-force-challenges-2026/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics