How CISOs Reduce Cyber Risk with MITRE ATT&CK
Nowadays CISOs face escalating threats that outpace traditional defenses. The strategy is evolving from compliance-driven checklists to a threat-informed approach. MITRE ATT&CK provides a globally accessible knowledge base of real-world adversary tactics, techniques, and procedures (TTPs), enabling organizations to understand, prioritize, and counter actual attacker behaviors rather than abstract controls.
This shift helps align security efforts with business realities: minimizing downtime, protecting revenue streams, safeguarding customer trust, and potentially lowering cyber insurance premiums through demonstrated proactive risk management.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Executive Summary
- Compliance-driven security measures control maturity, not adversary readiness. Threat-informed defense anchors risk management in real attack behaviors, which is where actual risk lives.
- MITRE ATT&CK provides the taxonomy, not the intelligence. The framework names and structures adversary techniques; organizations need curated, real-world threat data to make those techniques actionable.
- SOC workflow integration is non-negotiable. MITRE ATT&CK delivers risk reduction only when embedded into monitoring rules, triage processes, IR playbooks, and hunt methodologies.
- Speed of context determines security outcomes. Whether in triage or incident response, the time it takes to understand what a threat is doing directly determines how much damage it can cause. ANY.RUN’s Threat Intelligence Lookup and Sandbox compress that context-gathering from hours to seconds.
- Threat hunting requires real attack patterns, not just technique categories. Generic ATT&CK-based hunt queries produce noise; high-fidelity feeds of current attacker behavior produce findings.
- Risk reduction is measurable. MTTD, MTTR, MTTC, hunt yield rate, and false positive ratios are the business-level metrics that translate MITRE ATT&CK investment into language boards and insurers understand.
Two Lenses, One Risk: Compliance vs. Adversary-Centered Approach
Traditional risk management often relies on vulnerability scanning, compliance audits (e.g., NIST, ISO), and static controls. It focuses on known weaknesses and regulatory requirements but frequently misses how attackers chain behaviors in live environments.
MITRE ATT&CK is adversary-centric and behavior-focused. It maps real-world TTPs across tactics like Initial Access, Execution, Persistence, and Impact. This enables gap analysis, threat modeling, and measurable improvements in detection and response.
<thead> <tr>
<th>
Dimension </th>
<th>
Traditional Risk Management </th>
<th>
MITRE ATT&CK Approach </th>
</tr>
</thead><tbody> <tr>
<td>
Risk Basis </td>
<td>
Regulatory requirements & audit findings </td>
<td>
Real-world adversary techniques & behaviors </td>
</tr>
<tr>
<td>
Threat Model </td>
<td>
Generic, category-level threats </td>
<td>
Specific ATT&CK tactics, techniques, sub-techniques </td>
</tr>
<tr>
<td>
Detection Focus </td>
<td>
Signature-based, perimeter controls </td>
<td>
Behavioral analytics across the kill chain </td>
</tr>
<tr>
<td>
Measurement </td>
<td>
Control maturity, audit pass/fail </td>
<td>
Detection coverage mapped to ATT&CK matrix </td>
</tr>
<tr>
<td>
Response Approach </td>
<td>
Incident → remediation → compliance update </td>
<td>
Continuous detection, hunt, iterate </td>
</tr>
<tr>
<td>
Business Language </td>
<td>
Risk scores, audit gaps </td>
<td>
Mapped MITRE techniques tied to business impact </td>
</tr>
<tr>
<td>
Tooling </td>
<td>
GRC platforms, scanners </td>
<td>
SIEM + EDR + Sandbox + TI Feeds </td>
</tr>
</tbody></table>
The most important takeaway from this comparison is not that compliance is worthless. It isn’t. Regulatory requirements create accountability, force documentation, and establish minimum hygiene floors that matter for smaller organizations with limited resources. The problem arises when compliance becomes the ceiling rather than the floor.
Where Strategy Meets Reality: Making MITRE ATT&CK Operational
MITRE ATT&CK is not a product. It does not detect threats. It does not alert your analysts, contain attackers, or generate threat intelligence. The organizations that extract real risk reduction from MITRE ATT&CK are those that connect the framework’s taxonomy directly to how their SOC actually operates: the tools analysts use, the data they see, the workflows they follow under pressure.
<thead> <tr>
<th>
SOC Workflow </th>
<th>
What MITRE Provides </th>
<th>
What SOC Actually Needs </th>
<th>
How ANY.RUN Bridges the Gap </th>
</tr>
</thead><tbody> <tr>
<td>
Monitoring </td>
<td>
Identify techniques to watch </td>
<td>
Alerts linked to ATT&CK IDs </td>
<td>
TI Feeds: live IOC & technique feeds; Sandbox: real-time detonation signals </td>
</tr>
<tr>
<td>
Triage </td>
<td>
Explain technique & impact </td>
<td>
Fast analyst context on behavior </td>
<td>
TI Lookup: instant technique context + related samples; Sandbox: behavioral report </td>
</tr>
<tr>
<td>
Incident Response </td>
<td>
Provide structural framework </td>
<td>
Full execution context to contain </td>
<td>
Sandbox: full process tree, network, registry; TI Lookup: lateral movement history </td>
</tr>
<tr>
<td>
Threat Hunting </td>
<td>
Suggest what to search for </td>
<td>
Real attack patterns as hypotheses </td>
<td>
TI Feeds: emerging technique clusters; TI Lookup: hunt pivot on IOCs & TTPs </td>
</tr>
</tbody></table>
1. Eyes Wide Open: Enhancing Monitoring for Early Threat Detection
MITRE ATT&CK is a powerful compass for monitoring strategy. It tells defenders which techniques adversaries use during specific phases of an attack. T1566 (Phishing) for initial access, T1055 (Process Injection) for defense evasion, T1021 (Remote Services) for lateral movement, etc. Security teams can use the framework to build detection hypotheses, design SIEM rules, and prioritize which telemetry sources to collect.
What the SOC Actually Needs
The value of monitoring emerges from early visibility to enable swift action, reducing dwell time and limiting blast radius. Analysts need alerts with sufficient fidelity and timeliness to intervene while the attack is still in progress. That requires not just knowing which techniques exist, but understanding the current threat landscape: which groups are active, which malware families are being deployed this week, and which detection signatures are already stale.
Solution: Stay Current with Live Threat Feeds to Cut Detection Lag
Threat Intelligence Feeds provide continuously updated, machine-readable threat intelligence stream of IOCs (indicators of compromise) with malware family tags derived from real detonations in ANY.RUN’s Interactive Sandbox. Security teams can pipe these feeds directly into their SIEM or EDR, ensuring that MITRE-mapped detection rules stay current with actual adversary activity.
Business objective: Cut MTTD for novel threats. Increase the ratio of high-fidelity alerts to total alerts, lowering analyst alert fatigue and improving coverage of emerging attack vectors.
Reduce breach impact, not just detect threats.
Fuel MITRE ATT&CK with real-time intelligence and full attack visibility.
2. Speed Matters: Accelerating Triage with Behavioral Context
MITRE maps alerts to techniques, but analysts need rapid understanding of intent, impact, and validity to avoid alert fatigue. An alert tagged T1059.001 (PowerShell) tells an analyst that the technique involves command and scripting interpreter abuse. T1112 (Modify Registry) points to potential persistence or defense evasion. This context is valuable. But it is the starting point, not the destination.
What the SOC Actually Needs
Analysts dealing with hundreds of alerts per shift cannot afford multi-minute pivot chains to understand whether a flagged PowerShell execution is a legitimate IT automation script or the first stage of a ransomware deployment. They need behavior and impact context fast: What did this process actually do? Has this file hash or domain been seen in confirmed malicious activity?
Solution: Reduce MTTD with Full Attack Visibility inside a Sandbox
Threat Intelligence Lookup is a searchable threat data repository built on ANY.RUN’s analysis history. Analysts can query file hashes, IPs, domains, URLs, and process names and instantly surface related sandbox reports with MITRE ATT&CK mappings, malware family attributions, and associated threat actor context.
During triage, analysts can answer the key questions before escalating: Is this a known threat? What does it do? Which ATT&CK techniques are involved? What is the likely impact?
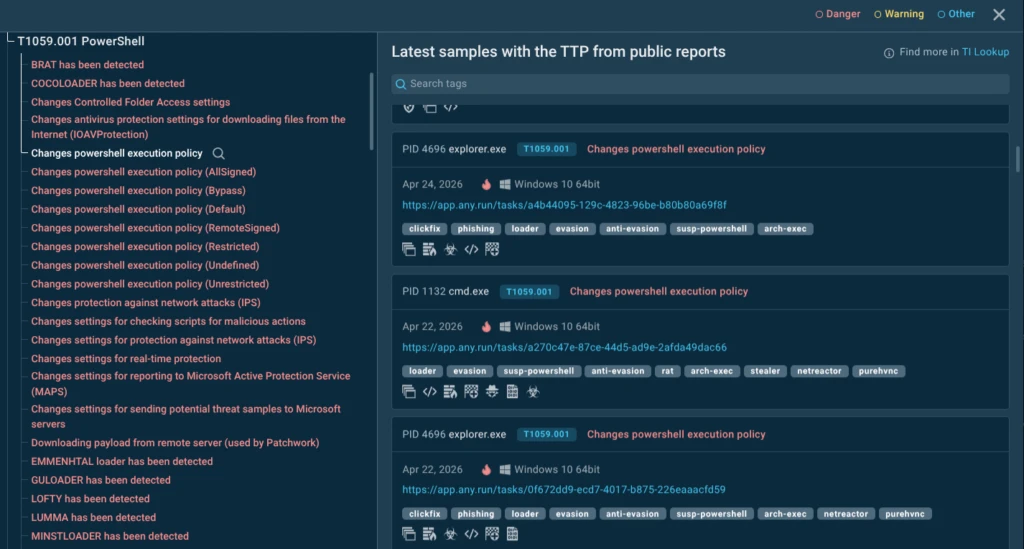 ANY.RUN Intelligence linking ATT&CK techniques to malware samples and behaviors
ANY.RUN Intelligence linking ATT&CK techniques to malware samples and behaviors
Interactive Sandbox complements TI Lookup for unknown samples. If an URL yields no TI Lookup match, analysts can submit it to the sandbox and receive a full behavioral report (process tree, network activity, file system changes, and ATT&CK technique tags) in minutes.
Unlike automated sandboxes that process samples silently, ANY.RUN lets analysts interact with the execution — clicking through prompts, observing network connections, and watching process trees unfold — while the sandbox maps every observed behavior to MITRE ATT&CK techniques in real time.
 Attack techniques detected in ANY.RUN sandbox detonation
Attack techniques detected in ANY.RUN sandbox detonation
Business objective: Reduce mean triage time per alert. Decrease false positive escalations. Increase analyst capacity without headcount growth, enabling the SOC to handle greater alert volume at the same staffing level.
3. Incident Response: From Labels to Action
MITRE ATT&CK gives incident responders a structured model for understanding what an adversary may have done across the kill chain. It offers a common language and playbooks for containment, full visibility into attacker actions for precise, minimal-disruption response. This is genuinely valuable for architecting investigations and communicating findings to stakeholders.
What the SOC Actually Needs
During an active incident, responders need execution context. Which processes ran? In which order? What registry keys were modified? Which files were dropped and where? Which internal hosts did the malware beacon to? Without this granular execution responders end up remediating visible symptoms while the attacker maintains persistence through overlooked footholds.
Turn MITRE ATT&CK into measurable risk reduction.
Use ANY.RUN to detect threats earlier and respond faster.
Solution: Compress Containment Time with Complete Execution Context
Interactive Sandbox generates a complete execution timeline for any submitted sample: full process trees (parent/child relationships, command-line arguments), all network connections (DNS queries, HTTP/S requests, C2 communication patterns), file system changes (created, modified, deleted files), and registry modifications.
Every action is timestamped and tagged with the corresponding MITRE ATT&CK technique. Responders don’t need to reconstruct what malware did from endpoint telemetry alone. They have a ground-truth behavioral record from a controlled detonation.
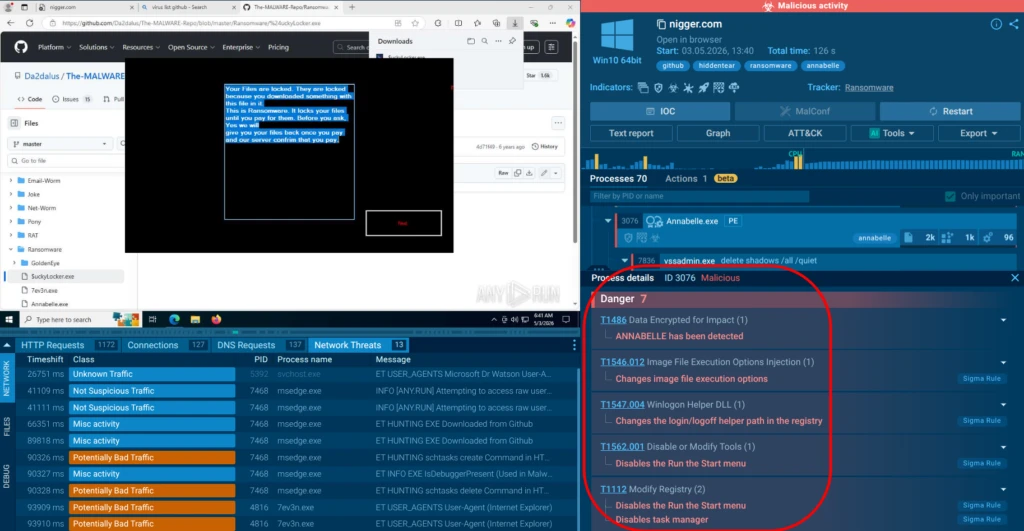 Processes mapped to MITRE ATT&CK techniques in a sandbox detonation
Processes mapped to MITRE ATT&CK techniques in a sandbox detonation
TI Lookup accelerates the lateral movement investigation. If an incident involves a suspicious IP or domain used for C2, TI Lookup surfaces all previous ANY.RUN analyses involving that indicator. It helps reveal which malware families have used it, when, and in what context.
Business objective: Reduce mean time to contain (MTTC) by giving responders complete execution context at the start of an investigation. Decrease re-infection rates by ensuring all persistence mechanisms are documented and remediated. Reduce incident response costs by compressing investigation timelines.
4. Proactive Defense: Supercharging Threat Hunting with Real Patterns
Threat hunting (proactively searching for adversary presence that evaded automated defenses) is where MITRE ATT&CK suggests hypotheses: if you are in a financial services organization, groups like FIN7 or Carbanak are relevant threats; their documented techniques (T1059, T1027, T1547) suggest where to look in your telemetry. This starting point is invaluable.
What the SOC Actually Needs
A successful hunt requires more than “look for PowerShell abuse”. It requires the specific parent-child process relationships, the exact command-line patterns, the particular registry keys, the network destinations that real-world attackers targeting your industry have actually used recently. Generic ATT&CK-based hunt queries produce excessive noise and burn hunter time on false leads. Real attack patterns are the fuel that makes hunts productive.
Solution: Turn Hunt Hypotheses into High-Yield Findings with Real Attacker Patterns
Threat Intelligence Lookup enables hunt pivoting at scale. A hunter who identifies a suspicious process name can query TI Lookup to find all samples that share that process, discover related IOCs, identify the malware family, and extract the precise command-line patterns that family uses. This turns a single hunt lead into a comprehensive behavioral profile needed to write high-confidence hunt queries.
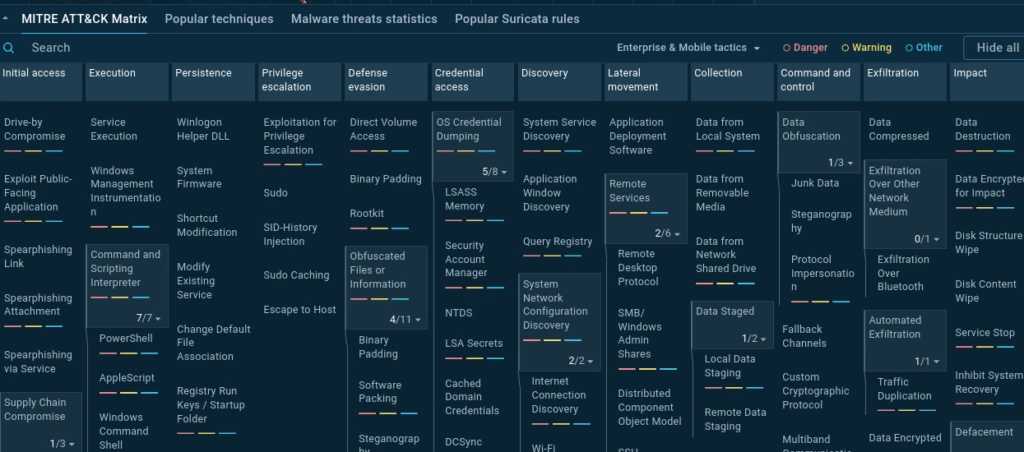 MITRE ATT&CK matrix in ANY.RUN’s TI Lookup
MITRE ATT&CK matrix in ANY.RUN’s TI Lookup
The combination of TI Feeds and TI Lookup transforms threat hunting from a creative exercise into an evidence-based discipline grounded in real adversary behavior.
Business objective: Increase the yield rate of threat hunts (confirmed findings per hunt hour). Identify attacker dwell time earlier, reducing the average time an adversary operates undetected inside the network. Demonstrate proactive risk reduction to board and audit stakeholders.
Conclusion: From Framework to Force Multiplier
MITRE ATT&CK has fundamentally changed how the security industry thinks about risk: from abstract control gaps to concrete adversary behaviors. For CISOs, this shift represents an opportunity to speak a language that resonates equally in the boardroom and the SOC: the language of what attackers actually do, and how prepared your organization is to detect, contain, and recover.
Make every SOC workflow count toward business protection.
Connect MITRE ATT&CK with live actionable threat data.
But the framework’s potential is only realized when it is connected to operational reality. MITRE ATT&CK without actionable threat intelligence is a map without territory. The SOC workflows that matter (monitoring, triage, incident response, and threat hunting) all require real-world adversary data to function at the speed and fidelity modern threats demand.
ANY.RUN’s threat analysis and intelligence products are purpose-built to close this gap. Together, they transform MITRE ATT&CK from a conceptual framework into an operational engine that drives measurable risk reduction across every phase of the security operations cycle.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams detect, investigate, and respond to threats faster.
ANY.RUN solutions include Interactive Sandbox, Threat Intelligence Lookup, Threat Intelligence Feeds, and integrations for SOC workflows across SIEM, SOAR, EDR, and other security tools. Together, they help teams safely analyze suspicious links, files, and scripts, uncover phishing behavior, trace credential theft and remote access activity, and enrich investigations with real-world threat context.
Built for security-conscious organizations, ANY.RUN is SOC 2 Type II attested and supports enterprise-ready controls such as SSO, MFA, granular privacy settings, and AES-256-CBC encryption.
Trusted by more than 15,000 organizations and 600,000 security professionals worldwide, ANY.RUN gives SOC teams the visibility they need to move from uncertain alerts to evidence-based decisions.
FAQ
Yes. Demonstrating ATT&CK-mapped controls, gap closures, and proactive testing provides evidence of mature risk management, which insurers often reward with lower premiums.
Detection coverage measures visibility into techniques; risk reduction quantifies business impact mitigation (e.g., prevented data loss or downtime) through layered defenses, response speed, and proactive measures.
Quarterly at minimum, or after major incidents, new threat actor campaigns, or significant environment changes. Continuous integration via feeds and hunting yields ongoing insights.
It complements them by adding adversary behavior details to NIST’s risk management processes, enabling more targeted control implementation and effectiveness measurement.
They provide real-world context, fresh IOCs/IOAs, and behavioral examples that make abstract TTPs immediately actionable in monitoring, triage, and hunting.
Begin with high-priority tactics relevant to your industry, map existing tools, use free ATT&CK Navigator, and incorporate accessible behavioral intelligence sources for quick wins in triage and response.
The post How CISOs Reduce Cyber Risk with MITRE ATT&CK appeared first on ANY.RUN's Cybersecurity Blog.
Article Link: How CISOs Reduce Cyber Risk with MITRE ATT&CK
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics
