CVE-2026-20093: Critical Cisco IMC Flaw Allows Unauthenticated Admin Access to UCS Servers
CVE-2026-20093: Critical Cisco IMC Flaw Allows Unauthenticated Admin Access to UCS Servers
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
CVE-2026-20093, is an authentication bypass flaw found in the change password functionality of Cisco Integrated Management Controller (IMC). It could allow an unauthenticated, remote attacker to bypass authentication mechanisms and gain unauthorized access to the system with Administrator privileges.
What Is CVE-2026-20093?
CVE-2026-20093 is a critical security flaw (CVSS score of 9.8) that affects the Cisco Integrated Management Controller (IMC), a management service for Cisco Unified Computing System (UCS) C-Series rack servers and some S-Series servers. The vulnerability is rooted in an Improper Input Validation issue (CWE-20) within the password change functionality of the IMC. This flaw allows an unauthenticated, remote attacker to completely bypass authentication and gain full administrative access to affected servers, providing deep, system-level control. The vulnerability was discovered and reported by security researcher “jyh.”
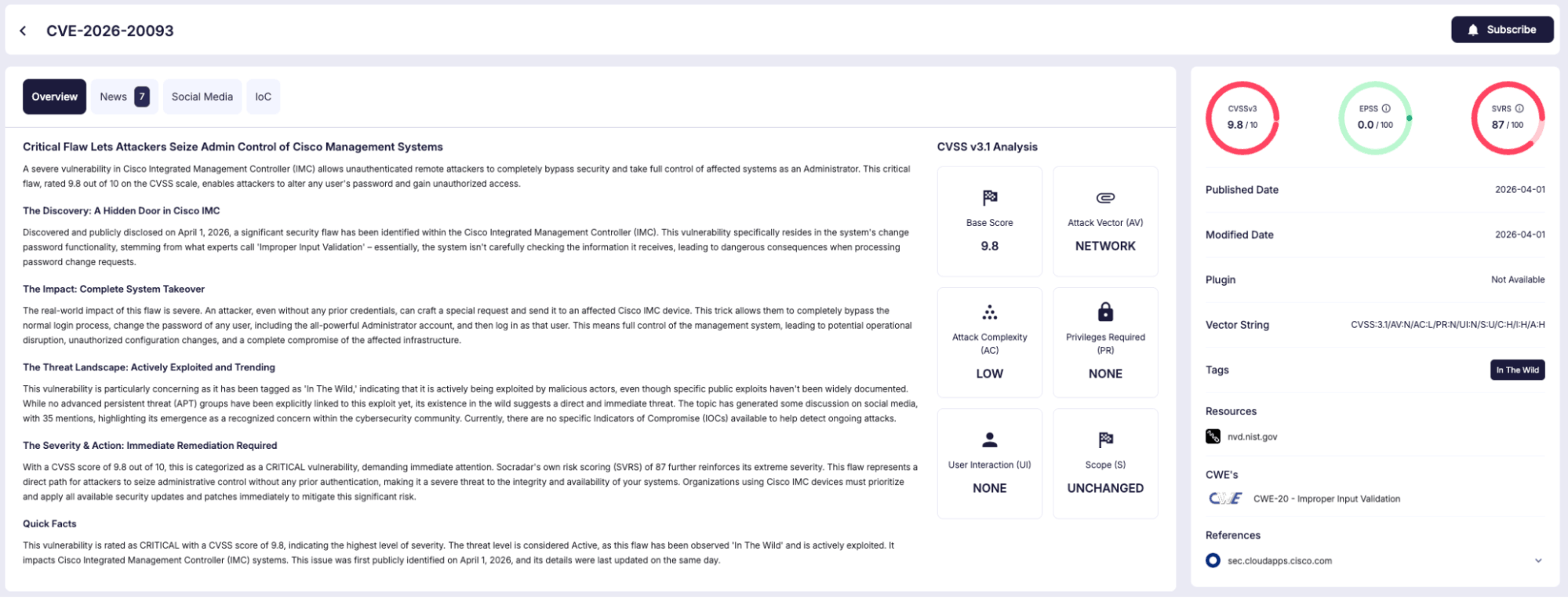
Details of CVE-2026-20093 (SOCRadar Vulnerability Intelligence)
Which Versions Are Affected and What Versions Fix It?
The vulnerability impacts a wide array of Cisco hardware when running a vulnerable release of Cisco IMC. Affected products include:
- 5000 Series Enterprise Network Compute Systems (ENCS)
- Catalyst 8300 Series Edge uCPE
- UCS C-Series M5 and M6 Rack Servers in standalone mode
- UCS E-Series Servers M3
- UCS E-Series Servers M6
Additionally, dozens of Cisco appliances built on preconfigured UCS C-Series servers are vulnerable if they expose access to the Cisco IMC UI:
- Application Policy Infrastructure Controller (APIC) Servers
- Business Edition 6000 and 7000 Appliances
- Catalyst Center Appliances
- Cisco Telemetry Broker Appliances
- Cloud Services Platform (CSP) 5000 Series
- Common Services Platform Collector (CSPC) Appliances
- Connected Mobile Experiences (CMX) Appliances
- Connected Safety and Security UCS Platform Series Servers
- Cyber Vision Center Appliances
- Expressway Series Appliances
- HyperFlex Edge Nodes
- HyperFlex Nodes in HyperFlex Datacenter without Fabric Interconnect (DC-No-FI) deployment mode
- IEC6400 Edge Compute Appliances
- IOS XRv 9000 Appliances
- Meeting Server 1000 Appliances
- Nexus Dashboard Appliances
- Prime Infrastructure Appliances
- Prime Network Registrar Jumpstart Appliances
- Secure Endpoint Private Cloud Appliances
- Secure Firewall Management Center Appliances
- Secure Malware Analytics Appliances
- Secure Network Analytics Appliances
- Secure Network Server Appliances
- Secure Workload Servers
Note: The vulnerability does not affect UCS B-Series Blade Servers, UCS C-Series M7 and M8 Rack Servers in standalone mode, UCS C-Series Rack Servers with Fabric Interconnects in UCS Manager or Intersight Managed Mode (IMM), UCS S-Series Storage Servers, UCS X-Series Modular System and Unified Edge.
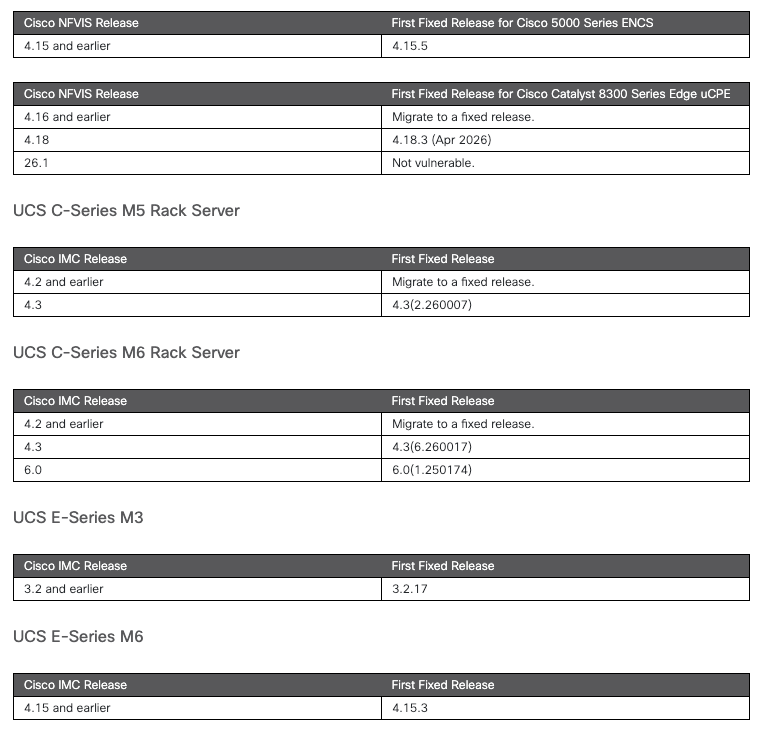
Fixed Releases by Cisco (caption)
Fixes: Cisco has released software updates to address the flaw. Depending on the hardware, fixed releases include IMC versions 4.3(2.260007), 4.3(6.260017), and 6.0(1.250174) for C-Series servers, as well as NFVIS updates like 4.15.5 and 4.18.3 for ENCS and Catalyst platforms.
How Does Exploitation Work in Real Deployments?
Exploitation is highly accessible as it features a low attack complexity and requires no prior privileges or user interaction.
An attacker exploits the flaw by sending a specially crafted HTTP POST request directly to the vulnerable device. Because the IMC fails to properly validate incoming password change requests, the attacker bypasses the internal authorization checks. This allows them to seamlessly reset and alter the password of any user account on the system, most notably the Admin user. Once the password is changed, the attacker can log in with full administrative privileges, effectively taking total control of the server infrastructure.
Is There Active Exploitation?
Currently, there is no evidence of active exploitation in the wild, nor is there any known public proof-of-concept (PoC) exploit code.
However, management controllers like the Cisco IMC are high-value targets for sophisticated threat actors, including ransomware gangs and APTs, because they provide a way to establish deep persistence independent of the host operating system.
What Indicators of Compromise Should Defenders Look For?
Traditional Endpoint Detection and Response (EDR) tools cannot see inside the IMC environment, meaning defenders must rely on robust log aggregation (like a SIEM). Security teams should monitor for the following:
- Unauthenticated HTTP Requests: Look for requests directed at password-change URIs that are not immediately preceded by a successful login event from the same IP address.
- Unexpected Password Resets: Any password change alerts for the ‘admin’ account that do not perfectly correlate with approved and scheduled maintenance windows should be treated as a critical incident.
- Anomalous Source IPs: Flag any management traffic or login attempts that originate from outside designated and trusted administrative subnets.
- Rogue Accounts: Audit the configured users on the IMC regularly to identify any new, unauthorized accounts an attacker might have created to maintain access.
What Should Security Teams Do Now?
Because there are no temporary workarounds available for this vulnerability, the only true fix is a firmware update. Security teams must take the following concrete steps:
- Inventory and Patch Immediately: Identify all UCS C-Series and E-Series servers, as well as appliances built on them that have exposed Cisco IMC interfaces, and upgrade the firmware to the fixed releases.
- Isolate the Management Plane: Baseboard management controllers (BMCs) like the IMC operate independently of the OS and should never be exposed to the public internet. Physically or logically isolate all IMC interfaces onto a dedicated, heavily firewalled management VLAN.
- Force Traffic Through Hardened Jump Hosts: Do not allow direct routing to the IMC network. Require administrators to authenticate through a hardened jump host equipped with multi-factor authentication (MFA) and session logging before they can interact with the management network.
- Configure SIEM for Specific Indicators: Standard endpoint detection and response (EDR) tools cannot see inside the IMC hardware. You must forward your IMC syslogs to a central SIEM and build custom alerts for the following events:
- HTTP requests hitting password-change URIs, especially if they are not immediately preceded by a successful login event from that exact IP address.
- Unexpected password resets targeting the admin account that do not align with an approved, scheduled maintenance ticket.
- Network traffic attempting to reach the IMC from any source IP outside of your explicitly trusted administrative subnets.
- Audit for Rogue Accounts: Because exploitation leaves few traces, manually audit the list of configured users on the IMC right now to ensure an attacker hasn’t already used the bypass to create a persistent backdoor account.
Article Link: https://socradar.io/blog/cve-2026-20093-cisco-imc-flaw/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics

