How Phishing Kits Targeting U.S. Giants Are Built, Sold, and Deployed
How Phishing Kits Targeting U.S. Giants Are Built, Sold, and Deployed
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Modern phishing kits can steal authenticated sessions from Microsoft 365 and Google accounts in real time, even when MFA is enabled, and access to those kits can cost as little as $120 for ten days. That low barrier to entry shows how far the Phishing-as-a-Service, or PhaaS, ecosystem has evolved. What was once a more limited criminal capability now operates at scale, with dedicated tooling, subscription models, customer support, and rapid infrastructure turnover.
By mid-2025, Tycoon 2FA alone accounted for 62% of all phishing attempts blocked by Microsoft, and it reportedly sent more than 30 million malicious emails in a single month to over 500,000 organizations. In parallel, the same open-source adversary-in-the-middle, or AiTM, frameworks are now used by both financially motivated actors and nation-state groups such as Russia’s Star Blizzard and Void Blizzard. This overlap has narrowed the distinction between espionage tooling and commodity cybercrime.
How Phishing Kits Bypass MFA: The AiTM Attack Explained
To understand why this ecosystem has become so effective, it is necessary to start with the technology itself. Modern phishing kits are far removed from the static HTML credential harvesters of a decade ago. Their main innovation lies in the AiTM architecture, which allows attackers to capture not just usernames and passwords, but also the authenticated session cookie created after a successful MFA challenge. In practice, that means the attacker does not need to defeat MFA directly. Instead, they intercept the session that MFA was meant to protect.
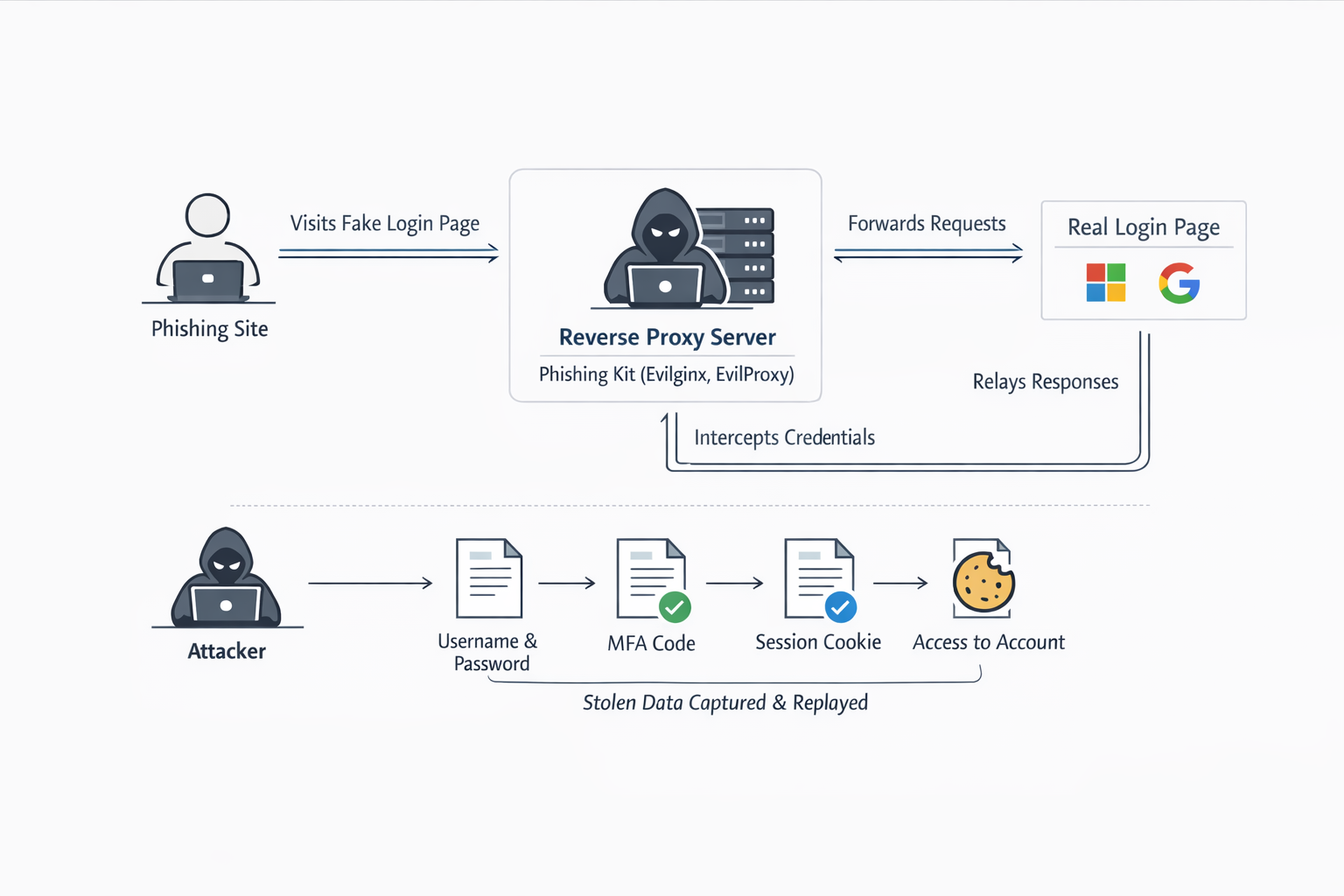
Two technical approaches dominate this space. The first is the reverse proxy model, used by kits such as Evilginx, EvilProxy, and NakedPages. In this setup, the phishing kit sits between the victim and the legitimate service. When the victim visits the phishing domain, the kit forwards requests to the real Microsoft or Google login page, then relays the responses back to the user. From the victim’s perspective, the login flow appears normal. In the background, however, the attacker captures every step in transit, including the username, password, MFA response, and resulting session cookie. Once that cookie is stolen, it can be replayed to access the account as an authenticated user. Evilginx, now at version 3 and written in Go, has even been noted as capable of bypassing Windows Hello for Business authentication.
Reverse proxy model
The second approach is more application-driven. Tools such as Tycoon 2FA, Sneaky 2FA, and Mamba 2FA present a cloned login page to the victim, while their backend submits the stolen credentials to the real authenticeation service. When the real service triggers an MFA prompt, the phishing page mirrors that same challenge. After the victim completes MFA, the kit captures the session cookie from the legitimate service’s response. This model shows that phishing kits are no longer simple copies of login pages. They are adaptive systems that interact with real authentication flows in real time. Tycoon 2FA illustrates this well. Its backend reportedly validates email addresses against Microsoft’s servers before the attack proceeds, then uses returned error messages to tailor the phishing flow to an organization’s specific security policies.
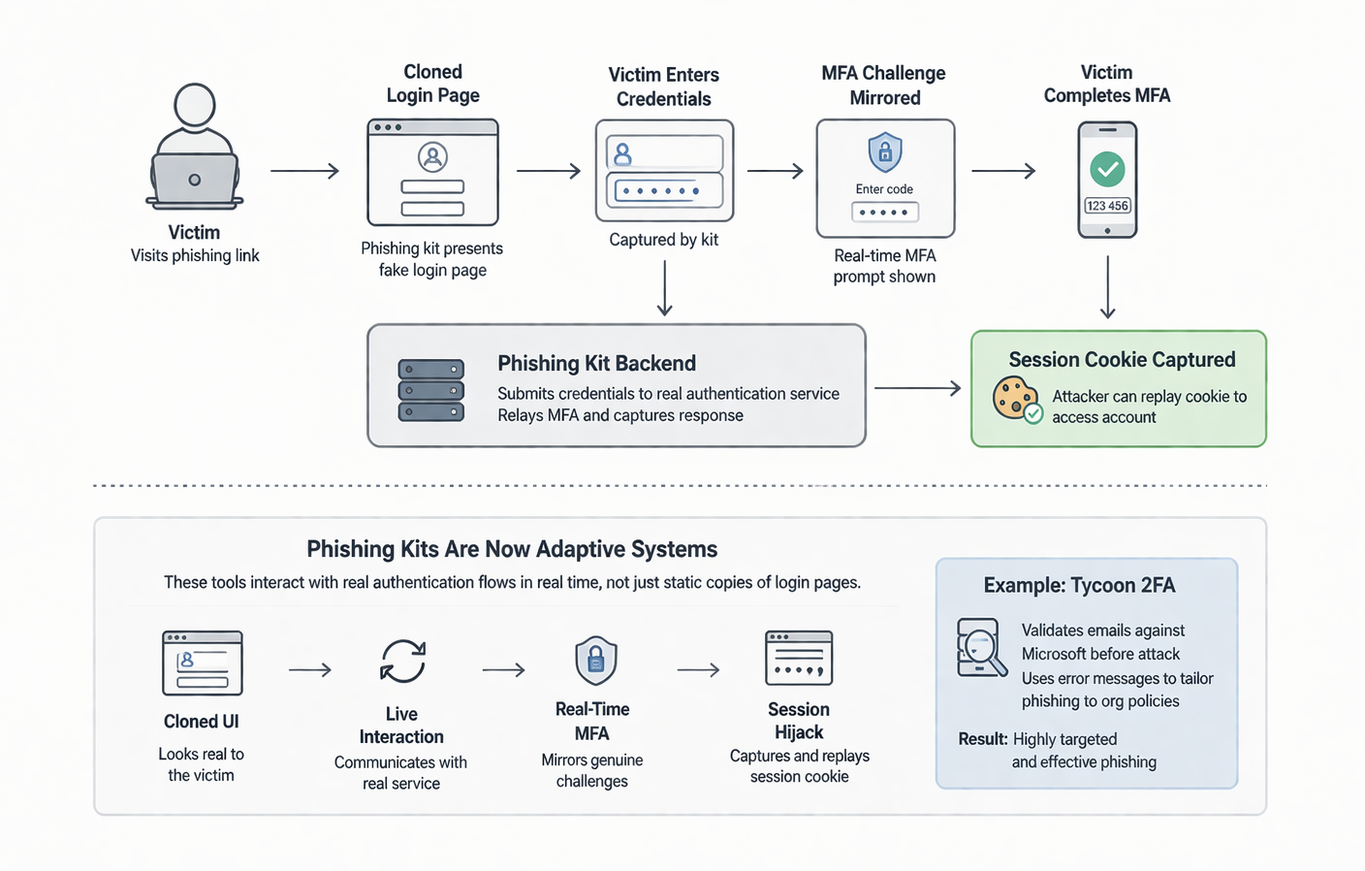
Application-driven Phishing Flow
In the reverse proxy model, the victim’s browser is effectively connected to the real service through the attacker’s server. The phishing kit acts as an intermediary that relays all traffic in real time. When the user enters credentials or completes MFA, those requests are forwarded to the legitimate service, and the responses are sent back to the user. This creates a single continuous session that passes through the attacker, allowing the kit to capture data as it moves between the victim and the service.
In contrast, the application-driven model separates these interactions into two distinct sessions. The victim only communicates with a fake login page, which collects the input locally. The phishing kit then uses this data to initiate its own session with the real authentication service. It submits the credentials, handles the MFA challenge, and receives the session cookie independently. This means the attacker is not relaying a live session but is instead reproducing the login process on behalf of the victim, with full control over how the authentication flow is executed and adapted.
Seen together, these techniques explain why MFA on its own might not be enough. The issue is not that MFA has stopped working. The issue is that these kits are designed to operate after MFA succeeds.
Phishing-as-a-Service (PhaaS): Pricing, Marketplaces, and Telegram Distribution
The technical strength of these kits would matter less if access to them remained limited. Instead, the opposite is true. The PhaaS market has made advanced phishing infrastructure available to a wide range of actors, including those with limited technical skill. That accessibility is one of the main reasons phishing kits have become such a persistent threat to major enterprises.
Today, the marketplace operates with the polish of legitimate SaaS businesses. Telegram has become the main sales, support, and update channel for many operators, even though access to premium services such as EvilProxy may still require vetting on underground forums. Operators maintain official Telegram channels with hundreds or thousands of subscribers, publish demo videos, announce feature updates, share changelogs, and handle user questions through ticketing systems or live chat. This kind of support model lowers friction for buyers and shortens the path from purchase to deployment.
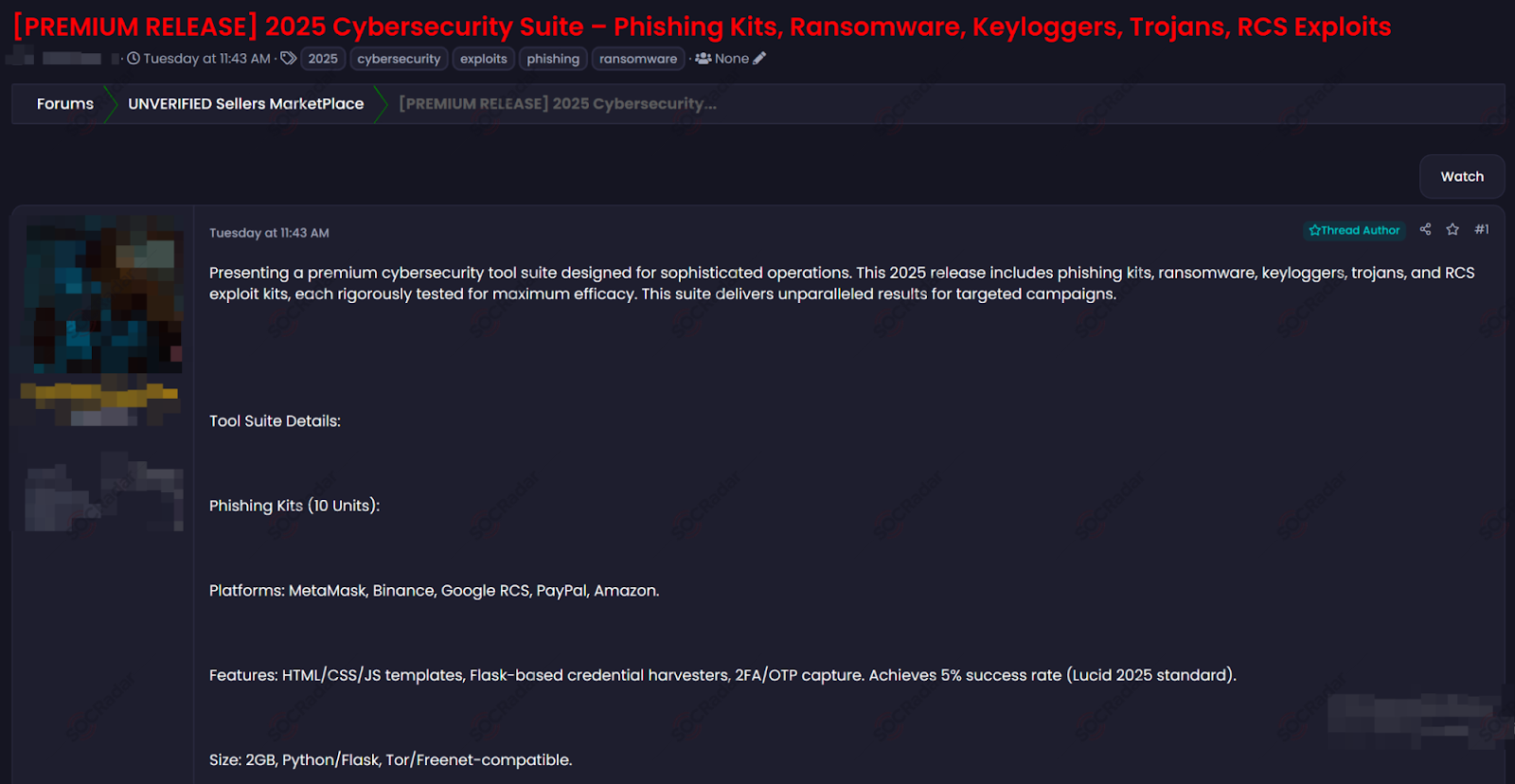
A threat actor selling phishing kits on a Dark Web Forum – SOCRadar Advanced Dark Web Monitoring
Pricing also follows familiar subscription patterns. Tycoon 2FA charges $120 for ten days and up to $350 per month. EvilProxy ranges from $150 to $600 per month, with pricing shaped partly by the target service, since Google account phishing commands a premium. W3LL Panel requires a $500 initial payment for three months, followed by $150 monthly renewals, and uses a token-based licensing model to reduce resale. Rockstar 2FA reportedly charged $200 for two weeks of access.
This commercial structure helps explain the resilience of the ecosystem. The market does not depend on a single operator or platform. When one tool loses infrastructure, another quickly absorbs demand. When one brand is disrupted, it often reappears under a different name. When forum-based distribution becomes risky, operators shift toward Telegram bots or other channels. In other words, phishing kits persist not only because they are effective, but also because the market around them is built to survive disruption.
Phishing Delivery Methods: Cloud Abuse, QR Code Phishing, and Email Vectors
Once these kits are built and sold, they still need to be delivered to victims. That is where infrastructure choices become central. Threat actors increasingly rely on trusted platforms and familiar services to improve delivery rates and reduce the chance of detection. This shift shows that modern phishing campaigns are shaped as much by distribution strategy as by credential theft itself.
One clear trend is the abuse of cloud infrastructure. Phishing incidents on Cloudflare Pages domains nearly tripled from 460 in 2023 to more than 1,370 in 2024, a 257% increase. Other widely trusted services, including Azure Blob Storage, Google Firebase, AWS CloudFront, and Amazon S3, have also hosted phishing assets. These environments offer several advantages to attackers. Victims see recognizable provider domains, TLS certificates are issued automatically, traffic patterns often appear normal, and security tools may treat those domains as lower risk. This makes trusted cloud infrastructure an attractive delivery layer for phishing operations. EvilProxy’s infrastructure, for example, has been traced to Cloudzy/RouterHosting LLC, which has been linked to the Iranian hosting company abrNOC and reportedly accepts cryptocurrency payments.
At the same time, email remains the main delivery vector, but it is no longer the only one worth tracking. Campaigns are diversifying, and QR code phishing is drawing more attention. The rise in reports related to QR-based phishing suggests that attackers are actively experimenting with formats that push users away from more heavily monitored desktop email workflows and onto mobile devices, where scanning a code can feel routine and less suspicious. This aligns with the broader logic of the ecosystem: trusted interfaces and familiar user behavior create better attack conditions.
Real-World Phishing Attack Examples: Scattered Spider, Nation-State Actors, and Enterprise Losses
The value of this ecosystem becomes clearer when looking at the actors that use it. Phishing kits are not abstract tools circulating in isolation. They are part of active operations carried out by both criminal groups and state-linked actors, and the victims include some of the largest organizations in the United States and beyond.
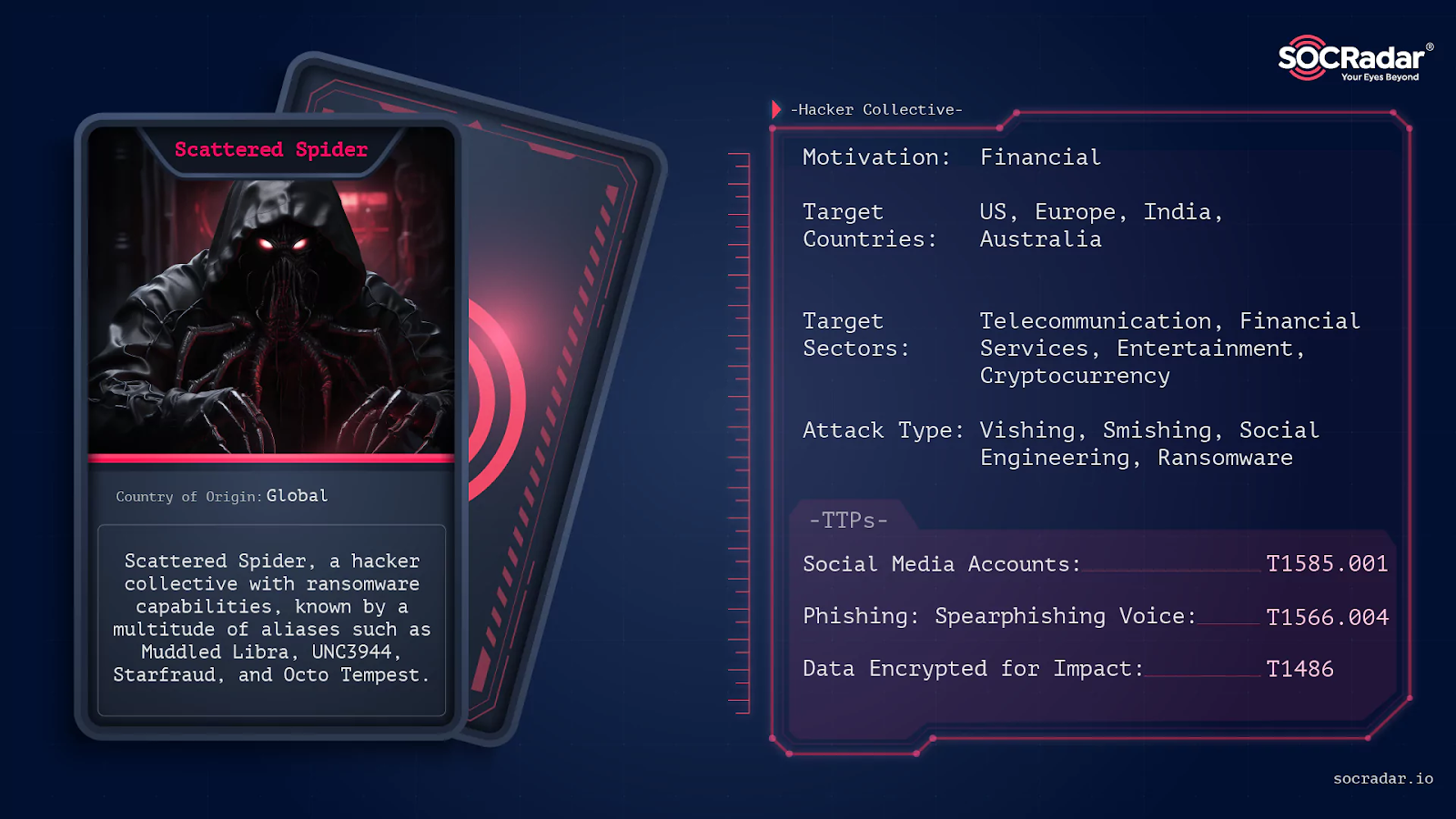
Scattered Spider, also tracked as UNC3944, remains one of the most visible groups using phishing-enabled access against major enterprises. Its September 2023 attack on MGM Resorts began with a ten-minute call to the IT help desk and escalated into ransomware deployment, with reported losses of about $100 million. Unofficial reporting also suggests that Caesars Entertainment paid a $30 million ransom following a similar intrusion during the same month. Beyond those cases, Scattered Spider has been linked to operations involving other major brands, including Nike, T-Mobile, Vodafone, Louis Vuitton, and multiple financial institutions. These incidents show how phishing activity can move quickly from credential theft to full operational disruption.
At the same time, nation-state groups have adopted many of the same tools. Star Blizzard, linked to the Russian FSB, has used Evilginx in AiTM spear-phishing campaigns targeting government officials, NGOs, and journalists. Microsoft and the U.S. Department of Justice seized more than 180 related domains in October 2024. Void Blizzard also used Evilginx, along with QR codes embedded in PDF attachments, to target more than 20 NATO-affiliated organizations. Microsoft captured the significance of this overlap in May 2025 when it noted that “the Evilginx phish kit has been used by multiple threat actors, from the prolific phishing operator Storm-0485 to the Russian espionage actor Star Blizzard.” That observation matters because it confirms a larger shift: the same tooling can now support both mass phishing campaigns and intelligence collection operations.
Law enforcement has responded with more aggressive disruption efforts, but the results remain mixed. The Interpol-coordinated 16shop takedown led to the arrest of three operators tied to a platform that had reportedly served 70,000 users across 43 countries. LabHost was dismantled in April 2024 through action spanning 19 countries, resulting in 37 arrests, and its developer later received an 8.5-year sentence. These operations have clearly imposed costs on the ecosystem. Even so, they have not removed the underlying market conditions that keep phishing kits available.
The financial impact helps explain why this remains a major issue. The FBI reported $2.77 billion in BEC losses for 2024 alone.
Conclusion
The phishing kit ecosystem targeting U.S. corporations has reached a level of maturity where its technology, pricing, support, and delivery models increasingly resemble legitimate software businesses. That maturity is what makes the threat so durable. These kits are not only powerful. They are easy to obtain, simple to operate relative to their impact, and supported by an ecosystem that adapts quickly under pressure.
Three developments define the current environment.
- First, AiTM-based MFA bypass is now a commodity feature available at low cost rather than a niche capability associated only with advanced actors.
- Second, Telegram has become a primary marketplace and support channel, which has made phishing infrastructure more accessible to a broader user base.
- Third, the convergence of criminal and state-sponsored tooling means the same Evilginx phishlet aimed at a Fortune 500 executive could be operated by a teenage affiliate, a financially motivated intrusion crew, or an intelligence officer.
Law enforcement has achieved important disruptions, including the dismantling of LabHost, arrests tied to Scattered Spider, and domain seizures associated with Tycoon 2FA. Still, the ecosystem’s ability to rebrand, rotate infrastructure, and shift distribution channels means that disruption windows are often measured in days rather than months. As a result, the defensive baseline has changed. Organizations can no longer treat MFA deployment as a sufficient endpoint. The focus now needs to include phishing-resistant FIDO2 authentication, continuous session monitoring, and detection strategies built on the assumption that the email gateway will not stop every malicious message.
Article Link: https://socradar.io/blog/phishing-kits-targeting-us-giants/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics