The Week in Vulnerabilities: OpenClaw, FreeBSD, F5 BIG-IP, and Critical ICS Bugs

Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Cyble Research & Intelligence Labs (CRIL) weekly vulnerability report tracked 1,960 vulnerabilities last week, reflecting a continued surge in vulnerability disclosures across enterprise and cloud ecosystems.
Of these, 248 vulnerabilities have publicly available Proof-of-Concept (PoC) exploits, significantly increasing the likelihood of real-world attacks and accelerating exploitation timelines.
Additionally, at least 5 vulnerabilities were actively discussed across underground forums, indicating strong attacker interest and rapid weaponization.
A total of 214 vulnerabilitieswere rated critical under CVSS v3.1, while 57 were rated critical under CVSS v4.0.
Furthermore, CISA added 4 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
On the industrial side, CISA issued 7 ICS advisories covering 10 vulnerabilities, impacting vendors such as Schneider Electric, WAGO, and PTC.
Weekly Vulnerability Report's Top 5 CVE's
CVE-2026-32917 — OpenClaw (Critical)
CVE-2026-32917 is a critical remote command injection vulnerability affecting OpenClaw, an AI agent framework.
The flaw occurs in the iMessage attachment staging workflow, allowing attackers to inject commands into remote systems. Successful exploitation enables arbitrary command execution, potentially leading to full system compromise.
CVE-2026-4747 — FreeBSD RPCSEC_GSS (Critical)
CVE-2026-4747 is a critical stack-based buffer overflow vulnerability in FreeBSD caused by improper bounds checking in packet handling.
Attackers can send specially crafted requests to trigger a stack overflow, resulting in remote code execution with kernel-level privileges, enabling full system takeover.
CVE-2026-31883 — FreeRDP (Critical)
CVE-2026-31883 is a heap-based buffer overflow vulnerability in FreeRDP’s audio decoding components.
A malicious RDP server or man-in-the-middle attacker can exploit this flaw to execute arbitrary code, potentially compromising remote desktop clients and enterprise environments.
CVE-2026-1207 — Django (High)
CVE-2026-1207 is a SQL injection vulnerability in Django applications using PostGIS RasterField lookups.
Insufficient input validation allows attackers to inject malicious SQL queries, leading to data exposure, modification, and potential lateral movement within backend systems.
CVE-2025-53521 — F5 BIG-IP APM (Critical)
CVE-2025-53521 is a critical vulnerability in F5 BIG-IP Access Policy Manager, initially classified as a DoS flaw but later reclassified as unauthenticated remote code execution following active exploitation.
This vulnerability allows attackers to gain full control of access management systems, posing significant risks to enterprise networks.
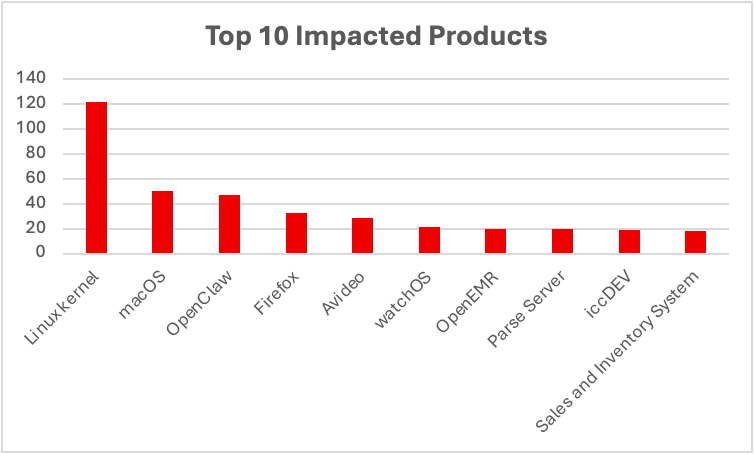 Data Source: Cyble Vision
Data Source: Cyble Vision
Vulnerabilities Added to CISA KEV
CISA continued expanding its KEV catalog, reflecting active exploitation trends.
Notable addition:
CVE-2025-53521 — F5 BIG-IP APM
Initially considered a denial-of-service flaw, it was reclassified as a remote code execution vulnerability after evidence of active exploitation emerged.
This shows how vulnerabilities can evolve in severity over time, reinforcing the need for continuous reassessment and monitoring.
Critical ICS Vulnerabilities
CISA issued 7 ICS advisories covering 10 vulnerabilities, with several rated critical.
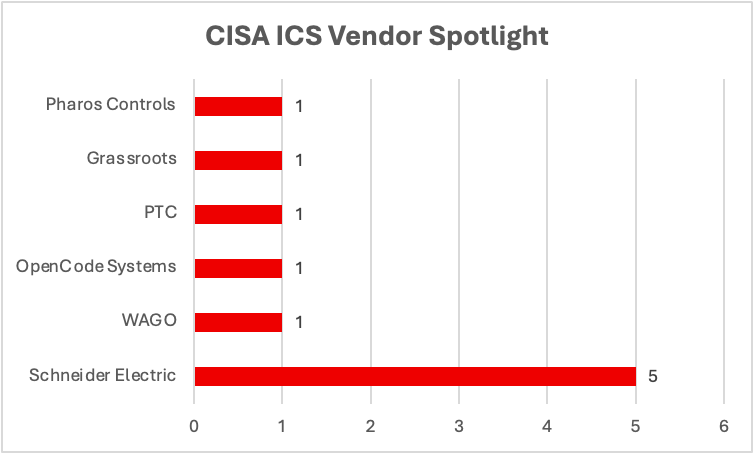 Data Source: Cyble Vision
Data Source: Cyble Vision
CVE-2026-2417 — Pharos Controls (Critical)
This vulnerability involves missing authentication for critical functions in Mosaic Show Controller firmware.
Attackers can exploit this flaw to gain unauthorized control over industrial systems, potentially disrupting operations.
CVE-2025-49844 — Schneider Electric Plant iT/Brewmaxx (Critical)
A use-after-free vulnerability in Schneider Electric’s industrial automation platform can lead to memory corruption and system compromise.
The presence of multiple vulnerabilities in this platform reflects systemic risk across widely deployed industrial environments.
CVE-2026-3587 — WAGO Managed Switches (Critical)
This vulnerability exposes hidden functionality in industrial switches, potentially enabling attackers to bypass controls and gain unauthorized access.
CVE-2026-4681 — PTC Windchill PDMLink (Critical)
This vulnerability involves improper control of code generation and currently has no available patch, leaving organizations exposed.
Grassroots DICOM (High, Unpatched)
A memory management flaw in Grassroots DICOM impacts healthcare imaging systems, with no vendor patch available, increasing risk to medical infrastructure.
Impacted Critical Infrastructure Sectors
Analysis shows that:
Commercial Facilities appear in 70% of ICS vulnerabilities
Critical Manufacturing and Energy each account for 60%
Healthcare, communications, and transportation sectors also face exposure.
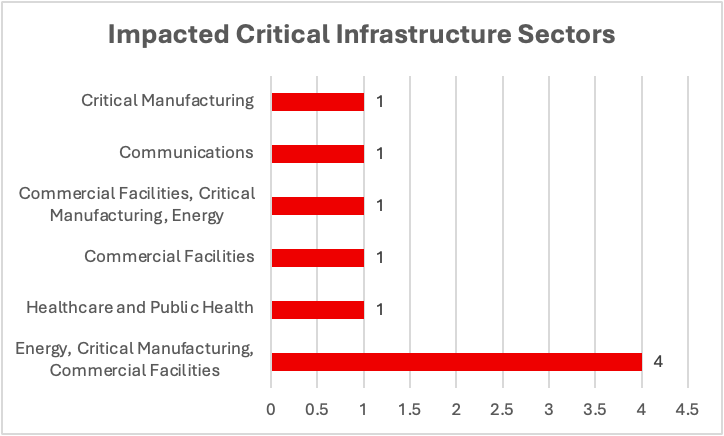 Data Source: Cyble Vision
Data Source: Cyble Vision
This distribution shows the strong cross-sector dependencies, where vulnerabilities in industrial platforms can cascade into multiple critical infrastructure domains.
Conclusion
This week’s findings highlight a convergence of:
- Increasing vulnerability volume and severity
- Rapid exploitation cycles driven by PoC availability
- Active underground discussion and weaponization
- Persistent weaknesses in industrial control systems
With 248 publicly available PoCs, KEV additions confirming active exploitation, and unpatched ICS vulnerabilities, organizations face significant risk across both enterprise IT and operational technology environments.
Key Recommendations
- Prioritize vulnerabilities based on exploit availability and operational impact
- Patch critical enterprise systems and externally exposed services immediately
- Implement strong input validation and secure coding practices
- Harden remote access and RDP environments
- Segment IT and OT networks to limit lateral movement
- Apply compensating controls for unpatched ICS vulnerabilities
- Continuously monitor threat intelligence and underground forums
- Conduct regular vulnerability assessments and penetration testing
Cyble’s attack surface management and vulnerability intelligence solutions enable organizations to identify exposed assets, prioritize remediation, and detect early indicators of compromise. By combining threat intelligence with proactive defense strategies, organizations can effectively mitigate evolving risks across enterprise and critical infrastructure environments
The post The Week in Vulnerabilities: OpenClaw, FreeBSD, F5 BIG-IP, and Critical ICS Bugs appeared first on Cyble.
Article Link: Weekly Vulnerability Report: OpenClaw, F5 BIG-IP & ICS Flaws
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics
