New SOC-Ready Reporting for Faster Triage, Escalation, and Incident Response with ANY.RUN
Successful SOC operations require more than accurate detections. Instant access to context, clear conclusions, and operationally relevant insights allow incidents to move across workflows without delays:
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
- During alert triage, analysts need a quick threat overview to decide on the next steps.
- Efficient incident response decisions demand clear, actionable context to rely on.
- Swift incident reporting requires cross-tier visibility without the need for manual processing of raw technical data.
Making ANY.RUN’s Interactive Sandbox a part of your standard SOC workflow helps eliminate bottlenecks that occur along the incident lifecycle by contributing to the optimization of each process, decision, and report.
SOC-ready Tier 1 reports turn complex sandboxing analysis into structured, decision-ready intelligence for faster, efficient triage, escalation, response, and reporting.
Executive Summary
- Whether operating as an internal SOC or delivering MDR and MSSP services, organizations need investigation workflows that scale efficiently under growing alert volumes.
- ANY.RUN’s Interactive Sandbox with Tier 1 Reports helps standardize triage, escalation, and incident reporting by becoming a decision-support layer for your security operations.
- Enterprise Suite teams can optimize sandbox investigations and reporting across the SOC at scale with unlimited Tier 1 report generation.
- The result is faster investigations, consistent escalations with less context lost, and optimized incident documentation for confident decisions and risk prioritization.
Challenges SOC Teams Face Today
With SOC teams continuously investigating suspicious files, URLs, phishing pages, and malware samples, turning the resulting massive volume of technical findings into actionable operational context fast enough to support efficient response becomes the key challenge.
The lack of standardized reporting leads to:
- Slow triage due to excessive manual work for Tier 1
- Higher pressure on Tier 2/3 and incident response team due to lack on ready-to-apply context
- Context loss during escalations and critical delays occur
- Additional burden falling on SOC managers without clear visibility into incident severity and business impact
ANY.RUN’s Interactive Sandbox already simplifies malware and phishing analysis through interactive, real-time investigation. Now, with Tier 1 Reports and AI Summary, it supports decision-making and reporting acrossSOC operations.
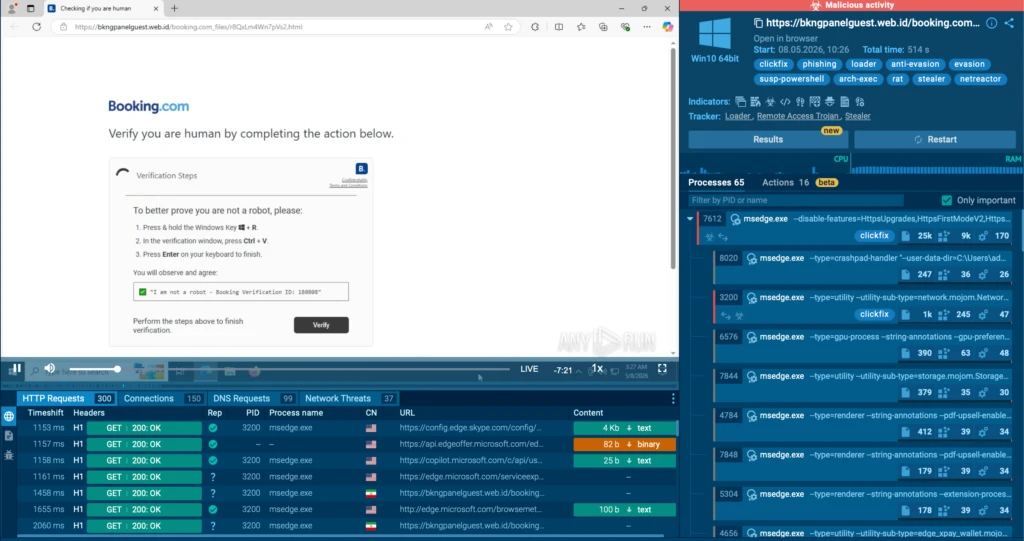 Phishing sample analysis in ANY.RUN Sandbox
Phishing sample analysis in ANY.RUN Sandbox SOC-Ready Reporting Built Into the Analysis Workflow
New Tier 1 reports are integrated into SOC workflows through and offer complete, structured documents with operationally useful insights.
Tier 1 report includes:
- A clear verdict on the analyzed sample
- AI Summary featuring threat classification and executive summary
- Key IOCs and behavioral indicators
- MITRE ATT&CK mapping
They can be generated directly within the Interactive Sandbox in a single click, making sandbox analysis immediately usable across operational workflows.
Clarity for analysts. Visibility for decision-makers.
Faster response across the SOC.
Use Case #1: Fast Threat Understanding for Tier 1 During Triage
Via Tier 1 reports featuring AI Summaries, ANY.RUN’s Interactive Sandbox provides immediate answers to the most critical questions that occur during alert triage:
- Is the sample malicious?
- What behavior indicates that?
- What type of threat is involved?
- What MITRE ATT&CK TTPs and IOCs are present?
- Does the incident require escalation?
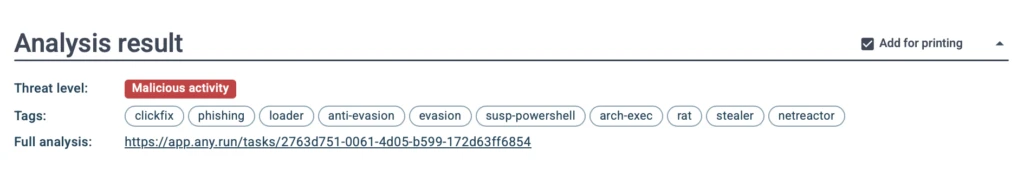 Threat verdict and tags at the top of Tier 1 reports already provide key info on the analyzed object
Threat verdict and tags at the top of Tier 1 reports already provide key info on the analyzed object Instead of manually reviewing raw technical data to answer these questions with confidence, the sandbox provides this context automatically in the form of a ready-to-use report that covers all findings into a clear operational document for fast and substantiated decision-making.
<thead> <tr>
<th colspan="2" rowspan="1">
ANY.RUN’s Interactive Sandbox & Tier 1 Reports </th>
</tr>
</thead><tbody> <tr>
<td>
Operational Impact </td>
<td>
Business Impact </td>
</tr>
<tr>
<td>
Faster alert validation </td>
<td>
Consistent triage quality </td>
</tr>
<tr>
<td>
Reduced manual enrichment </td>
<td>
Better <a href="https://any.run/cybersecurity-blog/soc-staff-shortage-burnout/" rel="noreferrer" target="_blank">analyst productivity</a> </td>
</tr>
<tr>
<td>
Fewer unnecessary escalations </td>
<td>
Reduced operational overhead </td>
</tr>
</tbody></table>
Use Case #2: Easy Access to Context for Tier 2, Tier 3, IR teams
In case of an escalation, Tier 2 analysts and incident responders frequently need to reconstruct investigation context manually before proceeding with containment.
Raw sandbox outputs take time to process and interpret, stretching investigation time and creating friction, as higher tiers essentially have to go back to triage stage for verification.
With Tier 1 reports, analysts get a structured information to pass on at the early stage, making ANY.RUN’s Interactive Sandbox more smoothly embedded into the entire investigation cycle, from triage to response.
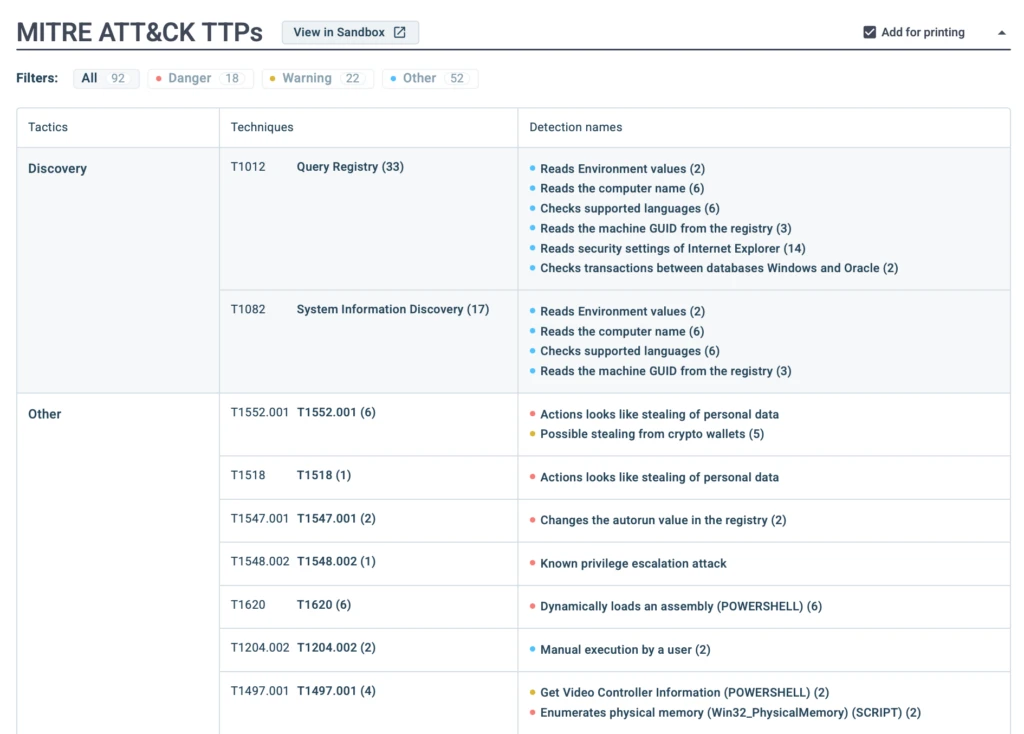 Clear breakdown of detected MITRE ATT&CK TTPs inside Tier 1 report
Clear breakdown of detected MITRE ATT&CK TTPs inside Tier 1 report <thead> <tr>
<th colspan="2" rowspan="1">
ANY.RUN’s Interactive Sandbox & Tier 1 Reports </th>
</tr>
</thead><tbody> <tr>
<td>
Operational Impact </td>
<td>
Business Impact </td>
</tr>
<tr>
<td>
Reduced friction during handoffs </td>
<td>
Better collaboration between teams </td>
</tr>
<tr>
<td>
No context lost in the process </td>
<td>
Full visibility for decision-makers </td>
</tr>
<tr>
<td>
Accelerated investigation pipeline </td>
<td>
Optimized operations across tiers </td>
</tr>
</tbody></table>
Use Case #3: Immediate Clarity for Decision-Makers
SOC managers, Heads of SOC, and CISOs don’t have time to review every technical artifact associated with an incident. Traditional reports may contain too many low-level details, whereas security leaders must assess the general business impact and urgency of a threat.
ANY.RUN’s Interactive Sandbox optimizes the hand-off workflow with a concise overview of the analysis in operational language suitable for leadership.
With AI Summary as part of the structure, the report explains what happened, why the object is malicious, which assets or systems may be at risk.
As a result, analysis outputs become standardized and practical, making them immediately usable for decision-making and internal communication.
<thead> <tr>
<th colspan="2" rowspan="1">
ANY.RUN’s Interactive Sandbox & Tier 1 Reports </th>
</tr>
</thead><tbody> <tr>
<td>
Operational Impact </td>
<td>
Business Impact </td>
</tr>
<tr>
<td>
Faster incident understanding </td>
<td>
Better executive visibility
Easier communication between teams |
Faster prioritization through clarity |
Consistent incident documentation |
Stronger operational governance |
Hands-On Case: Generating a Response-Ready Report on a Phishing Attack
In this phishing investigation, the Tier 1 report provides a clear, operational overview of the entire attack chain, helping both analysts and leadership quickly understand the threat severity and required response actions.
AI Summary further structures the findings into operationally relevant context suitable for triage, escalation, and internal communication:
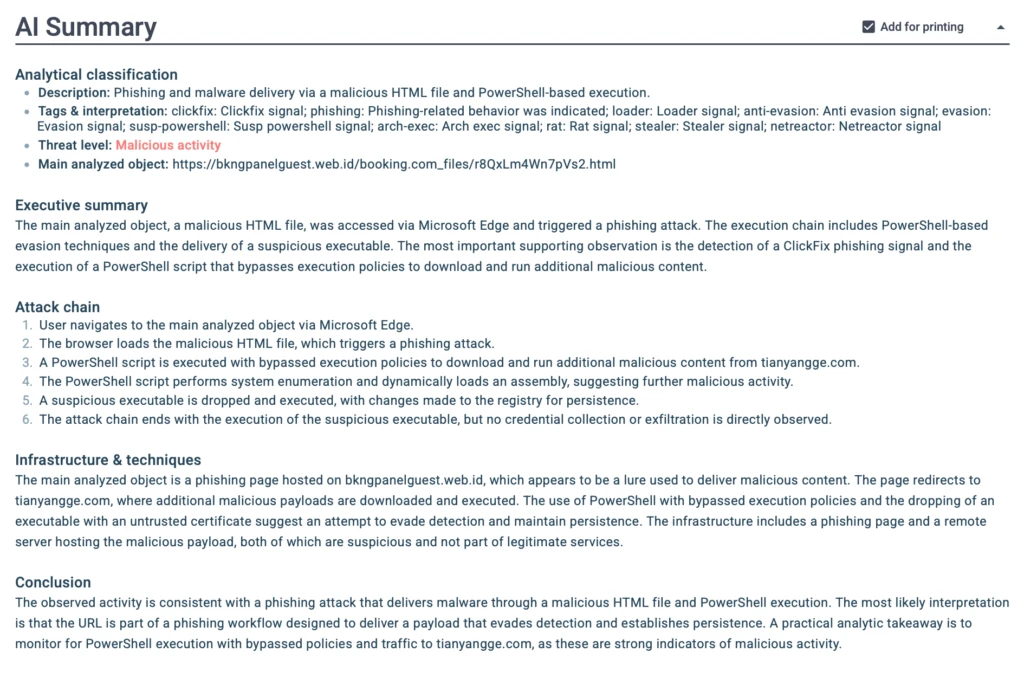 AI Summary providing a clear, structured overview of the threat
AI Summary providing a clear, structured overview of the threat The AI summary highlights the detection of a ClickFix phishing technique, followed by PowerShell execution with Execution Policy bypass attempts used to launch malicious activity on the host. It also outlines payload delivery behavior, subsequent system modifications, and persistence attempts through Windows Registry changes.
Instead of manually reconstructing the attack flow from raw sandbox telemetry, analysts receive a ready-to-use interpretation of the incident that can immediately support escalation and response workflows.
The complete attack chain, behavioral indicators, and resulting conclusions are already structured for operational use and are ready for further processing: escalation, IR hand-off, and containment.
Turn sandbox analysis into confident SOC decisions
with interactive investigations and refined reporting
Power Your SOC with ANY.RUNFrom Analysis to Action: Faster Escalations, Response, and Reporting
The new Tier 1 reports featuring AI Summary deliver direct operational value across the SOC:
- Faster Triage: Tier 1 analysts can quickly understand the nature of the threat and make confident decisions on whether to close or escalate alerts.
- Streamlined Escalation Process: Tier 2 and IR teams receive well-structured context instead of raw data, reducing handoff time and miscommunication.
- Accelerated Incident Response: Teams gain rapid visibility into attack behavior, helping reduce Mean Time to Respond (MTTR).
- Improved Internal Reporting: SOC managers and CISOs get consistent, professional summaries that are easy to read and share with stakeholders.
- More Consistent Performance: Standardized reports reduce quality variation between analysts and lower the risk of human error.
Unlimited access is available for Enterprise Suite and Hunter plans. Free plan users have a shared limit of 5 generations for both the Tier 1 report and AI Summary.
Conclusion
ANY.RUN’s new Tier 1 reports and AI Summary convert sandbox analysis outputs into structured, operationally ready documents that support every stage of the incident lifecycle, from initial triage to executive visibility.
Embedding Interactive Sandbox directly into a SOC workflow strengthens overall security operations maturity by allowing for faster and more confident decision-making across processes.
About ANY.RUN
ANY.RUN delivers cybersecurity solutions designed to support real-world SOC operations. They help security teams understand threats faster, make informed decisions, and operationalize threat intelligence across detection, investigation, and response workflows.
The company’s solutions include Interactive Sandbox for enterprise-grade malware analysis, as well as ANY.RUN’s Threat Intelligence with its modules Threat Intelligence Lookup and Threat Intelligence Feeds, providing continuously updated intelligence based on live attack analysis.
Used by over 15,000 organizations and 600,000 security professionals worldwide, ANY.RUN is SOC 2 Type II certified, ensuring strong security controls and protection of customer data.
Request access to ANY.RUN’s solutions →
FAQ
SOC-ready reports are sandbox analysis summaries that provide operational context for faster triage, escalation, incident response, and internal reporting.
No. While Tier 1 reports are designed to accelerate initial triage, they also support Tier 2, Tier 3, incident response teams, SOC managers, and CISOs by providing structured operational context, standardized reporting, and fast visibility into threat severity and business impact.
Tier 1 reports include a threat verdict, AI Summary, MITRE ATT&CK mapping, behavioral indicators, and IOCs generated directly from Interactive Sandbox analysis.
AI Summary converts technical sandbox findings into concise operational explanations that help analysts and decision-makers quickly assess threat severity, business impact, and required response actions.
Yes. ANY.RUN’s SOC-ready reporting helps standardize triage, escalation, and investigation workflows across internal SOC, MDR, and MSSP teams.
The post New SOC-Ready Reporting for Faster Triage, Escalation, and Incident Response with ANY.RUN appeared first on ANY.RUN's Cybersecurity Blog.
Article Link: SOC-Ready Reports for Faster Investigations by ANY.RUN
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics
