Dark Web Profile: Handala Hack
Dark Web Profile: Handala Hack
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
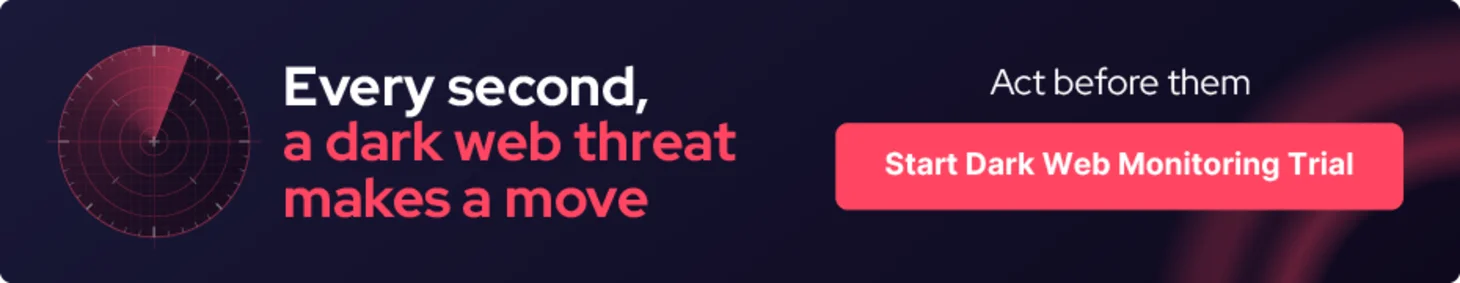
Not every hacktivist group is what it claims to be. Handala presents itself as a pro-Palestinian resistance collective, borrowing the name and imagery of a beloved political cartoon to position its operations as grassroots digital defiance. The reality, assessed with high confidence by multiple independent threat intelligence vendors, is considerably more serious: Handala is widely assessed to be a destructive cyber persona operated by Iran’s Ministry of Intelligence and Security (MOIS), not a spontaneous movement.
Since emerging in December 2023, the threat group has executed dozens of claimed attacks against Israeli and Western targets, deployed custom wiper malware against civilian infrastructure, and escalated to operations targeting U.S. corporations. Its most destructive claimed operation to date, a March 2026, Operation Epic Fury, attack on medical device company Stryker Corporation that reportedly wiped over 200,000 devices across 79 countries, signals a group that has moved well beyond the boundaries of conventional hacktivism.
Who Is Handala?
Handala (also stylized as Handala_hack) first appeared on December 18, 2023, launching both its Telegram channel and X/Twitter account simultaneously. The timing was deliberate: the group emerged weeks after the October 7, 2023 Hamas attack on Israel, positioning itself within the wave of pro-Palestinian hacktivist activity that followed. Its name references the iconic barefoot boy cartoon created by Palestinian political cartoonist Naji al-Ali in 1969, a symbol of steadfastness and resistance whose image has been appropriated wholesale across Handala’s branding, from defaced websites to Telegram propaganda.
Threat actor card of Handala Hack
Early channel posts referenced Hamas directly, with the group describing itself as “a small fighter” in the Hamas movement before pivoting to broader anti-Israel messaging. The branding is consistent and deliberate, designed to generate emotional resonance and establish credibility within the pro-Palestinian hacktivist ecosystem.
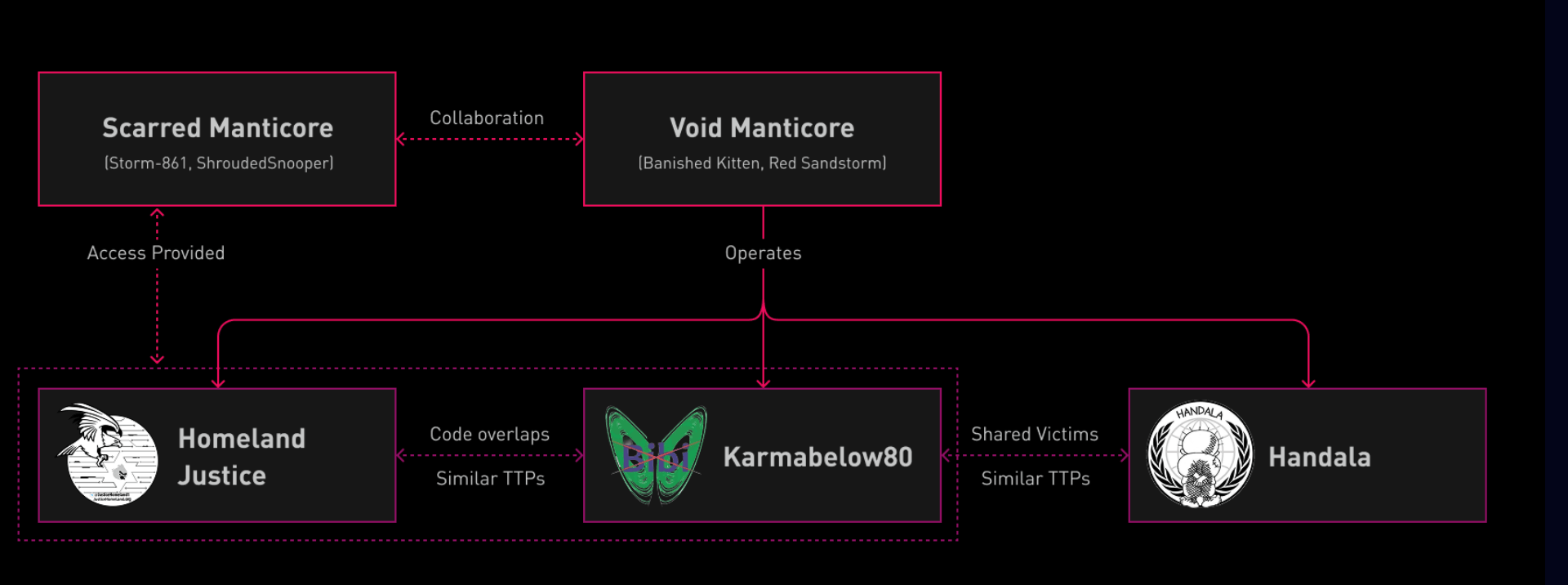
The attribution picture has hardened considerably over the past year. Check Point Research tracks the actor as Void Manticore, while other industry tracking systems identify the same activity cluster under names such as Storm-0842, BANISHED KITTEN, and Dune. Despite the different labels, reporting across the sector converges on MOIS affiliation rather than IRGC, an important distinction that separates Handala from operations such as CyberAv3ngers. Several analyses describe Handala as one of the most visible Iranian personas active in the current phase of the conflict, and independent investigations have repeatedly pointed to links with MOIS structures.
Who Operates Behind the Handala?
Elements of the group’s leadership have also surfaced publicly. Iranian researcher Nariman Gharib connected the operation to a cyber unit inside the MOIS counter-terrorism division led by Yahya Hosseini Panjaki, a deputy minister sanctioned by the U.S. Treasury in September 2024, later by the EU and the UK, and listed on the FBI terrorism watch list.
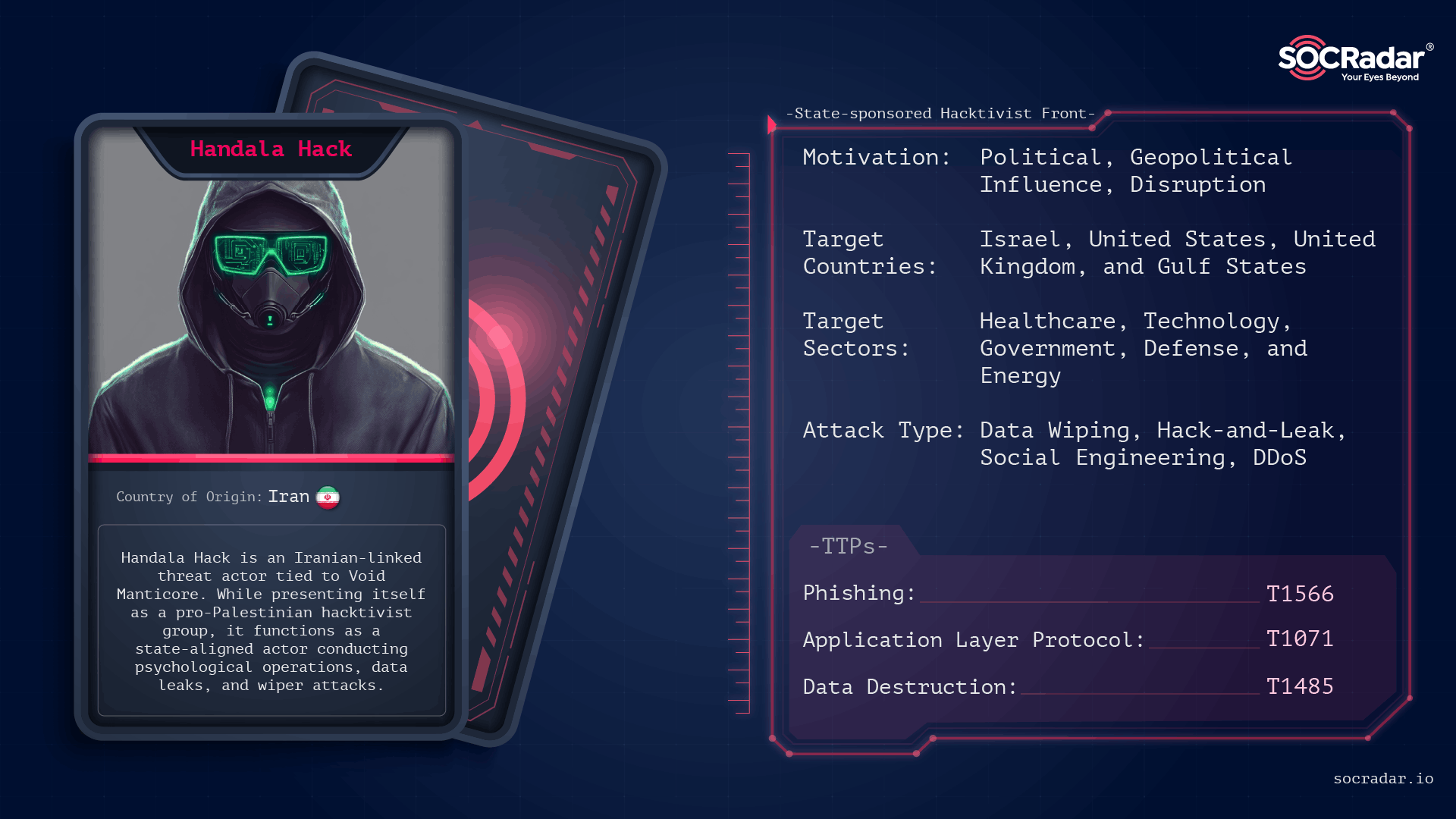
Mapping the Manticore threat network (Source: Check Point)
Operational reporting also indicates a structured division of labor between two actor clusters. Scarred Manticore (linked to activity associated with APT34/OilRig)typically establishes the initial foothold, frequently through vulnerabilities such as CVE-2019-0604 in Microsoft SharePoint, and conducts a period of intelligence collection. Access obtained during this phase, including web shells and Domain Admin credentials, is then transferred to Void Manticore and Handala Hack, which carries out the disruptive or destructive stage of the campaign. Comparable operational sequencing was observed during the 2022 cyberattacks on Albania conducted under the Homeland Justice persona, as well as in campaigns attributed to personas such as Karma and Handala.
Threat actor card for Void Manticore
This structure suggests a deliberate separation between access operations and the public-facing disruption campaigns. By presenting the latter through hacktivist-style online identities, destructive activity can be claimed and amplified for psychological impact while still preserving a layer of state deniability. The outward branding appears informal and ideological, but the operational tradecraft behind it reflects a far more organized capability.
What Are Handala’s Targets?
Handala’s targeting closely tracks geopolitical developments. While the majority of operations have focused on Israeli organizations, the scope has expanded since late 2025 to include U.S. companies, Gulf states, and Western institutions.
Handala operates a dedicated claim-and-propaganda website on both the clear web and Tor, where the group publicly announces alleged breaches, and issues ideological messaging targeting its adversaries.
By sector, technology is the most frequently targeted industry, followed by information technology, government and defense, critical infrastructure, energy, education, and financial. Researchers at Reichman University documented at least 85 claimed attacks between February 2024 and February 2025.
Geographically, Israel remains the primary focus. However, following the February 28, 2026 U.S.–Israeli strikes on Iranian targets (Operation Epic Fury), the group expanded its targeting. Claimed victims have included Jordan’s fuel infrastructure, Bank of Jordan, Sharjah Airport, Riyadh Bank, Israeli energy firms, and the Academy of the Hebrew Language, while Western organizations in the United States and United Kingdom have also faced increasing exposure.
Analysts caution that many of the group’s claims are likely exaggerated. Sophos X-Ops notes that Handala frequently overstates its capabilities, and some alleged breaches involve recycled or outdated data. Former Israeli National Cyber Directorate deputy head Rafael Franco described the group as a “loud actor” focused primarily on psychological and media impact rather than advanced technical sophistication.
Notable Operations
- CrowdStrike Outage Phishing Campaign (July 2024):
Following the global CrowdStrike Windows sensor outage that caused widespread BSOD failures, attackers launched a phishing campaign targeting Israeli organizations with fake remediation tools. Victims were directed to download a malicious archive containing a disguised installer that deployed a destructive wiper payload. The campaign used a multi-stage execution chain involving an NSIS installer, obfuscated scripts, and AutoIT loaders before triggering the final wiper stage. - Soreq Nuclear Research Center (September 2024): Handala claimed a breach and extraction of approximately 197 GB of classified nuclear project data. Israel’s National Cyber Directorate assessed this as primarily psychological warfare. The claim generated global headlines, but actual compromise remains unconfirmed.
- Israeli Police (February 2025): The group claimed exfiltration of 2.1 TB of data, including personnel records, weapons inventories, and psychological profiles of officers. Israeli police suggested a third-party vendor compromise. Published material was assessed as partially outdated.
Handala claims to have leaked Israel police documents on a hacker forum (SOCRadar Dark Web News)
- Kindergarten PA Systems (January 2026): Handala compromised Maagar-Tec emergency alert systems at over 20 kindergartens. Air raid sirens were activated and threatening Arabic messages were broadcast. This was one of the most psychologically impactful operations the group has conducted.

Screenshot of a post from the verified Hebrew news account ZiratNews on X (Twitter). The post, written in Hebrew, reports that hackers took control of about 20 children’s and youth emergency alert systems and played Arabic announcements or red alert sirens. It also claims an Iranian-backed group called Handala was responsible.
- Stryker Corporation (March 2026): Handala claimed it wiped over 200,000 systems and extracted 50 TB of data from the $25 billion medical device company, which holds $450 million in U.S. Department of Defense contracts. Stryker confirmed “severe, global disruption impacting all Stryker laptops and systems” in an SEC filing. Microsoft Intune MDM abuse was suspected as the delivery mechanism. This is the group’s most destructive operation to date.
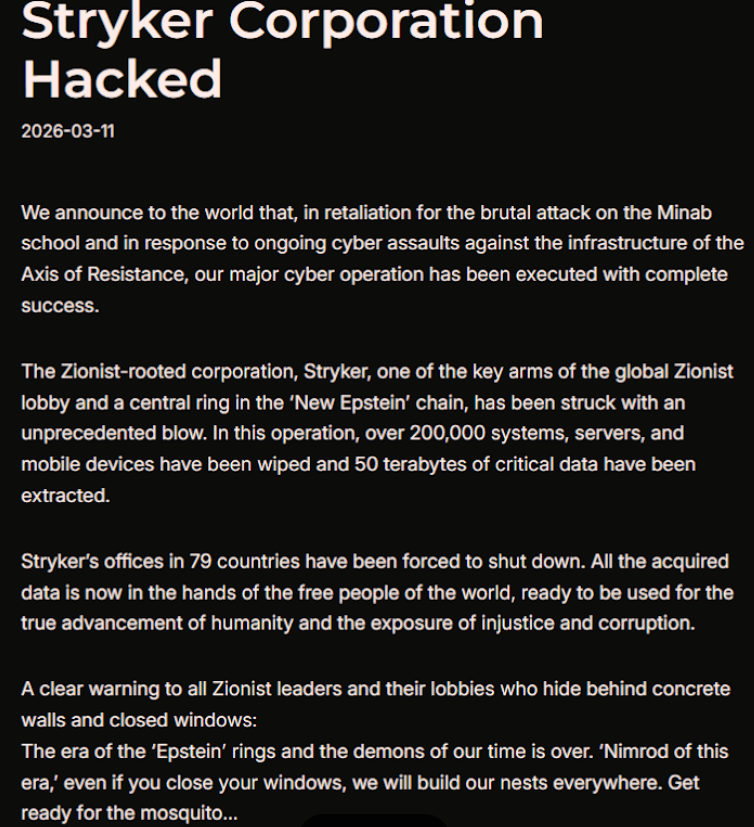
Handala Hack claims to have breached Stryker
- Verifone (March 2026): Handala claimed that it successfully hacked Verifone on March 11, 2026. The threat group alleged that it stole transaction and financial data and caused widespread disruptions across payment systems. They also shared several screenshots as proof of the intrusion.
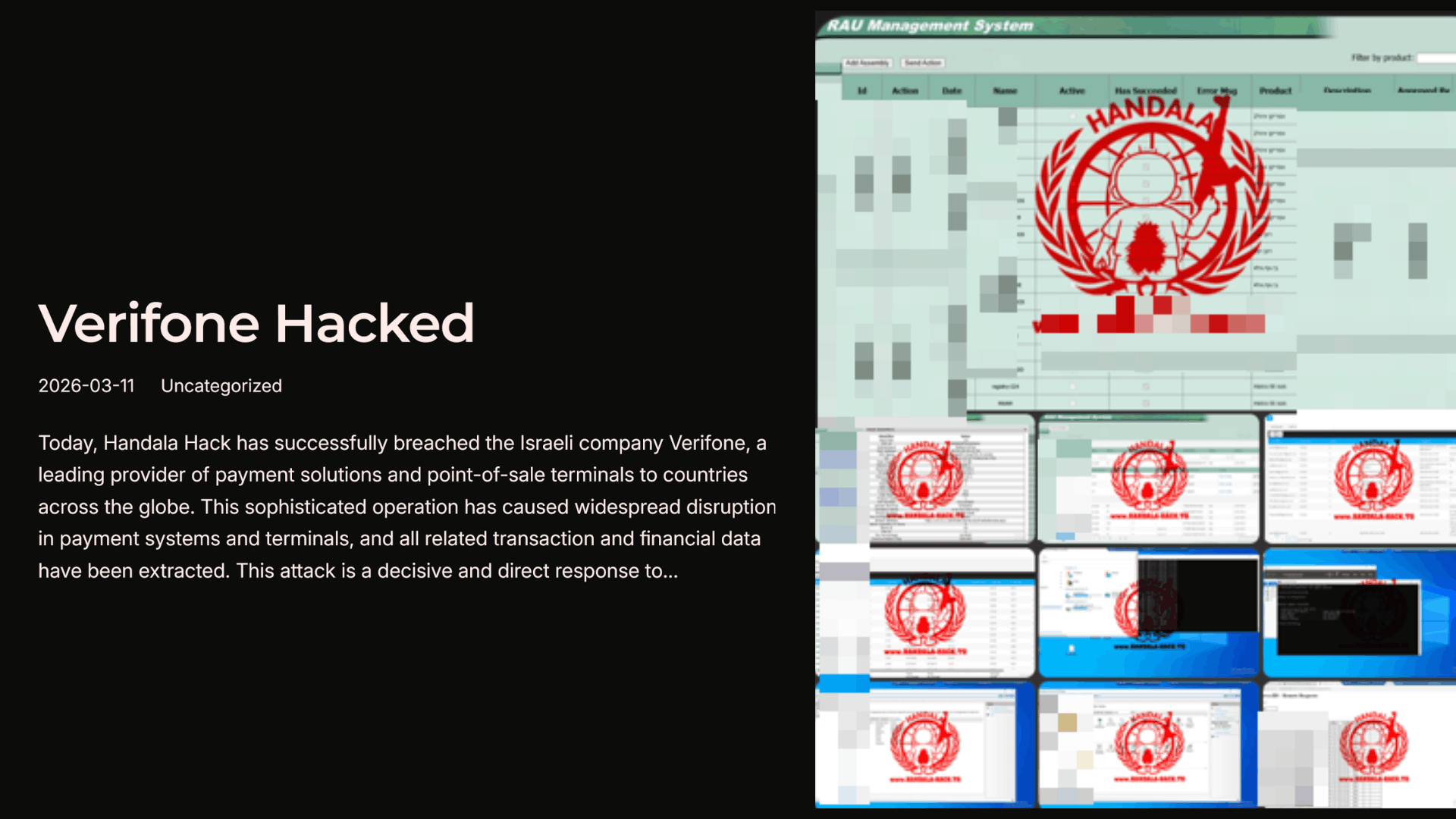
Handala Hack claims to have breached Verifone
What Techniques Does Handala Use?
Handala’s operations combine destructive malware, social engineering, and pragmatic intrusion techniques. Rather than relying on novel exploitation methods, the group integrates commercially available tools with custom payloads and living-off-the-land techniques to deliver destructive effects. This approach allows operators to maintain operational flexibility while supporting campaigns designed for disruption and psychological impact. The following attack chain is primarily derived from analysis of the July 2024 phishing campaign that exploited the global CrowdStrike outage, supplemented with observations from other Handala destructive operations between 2024 and 2026.
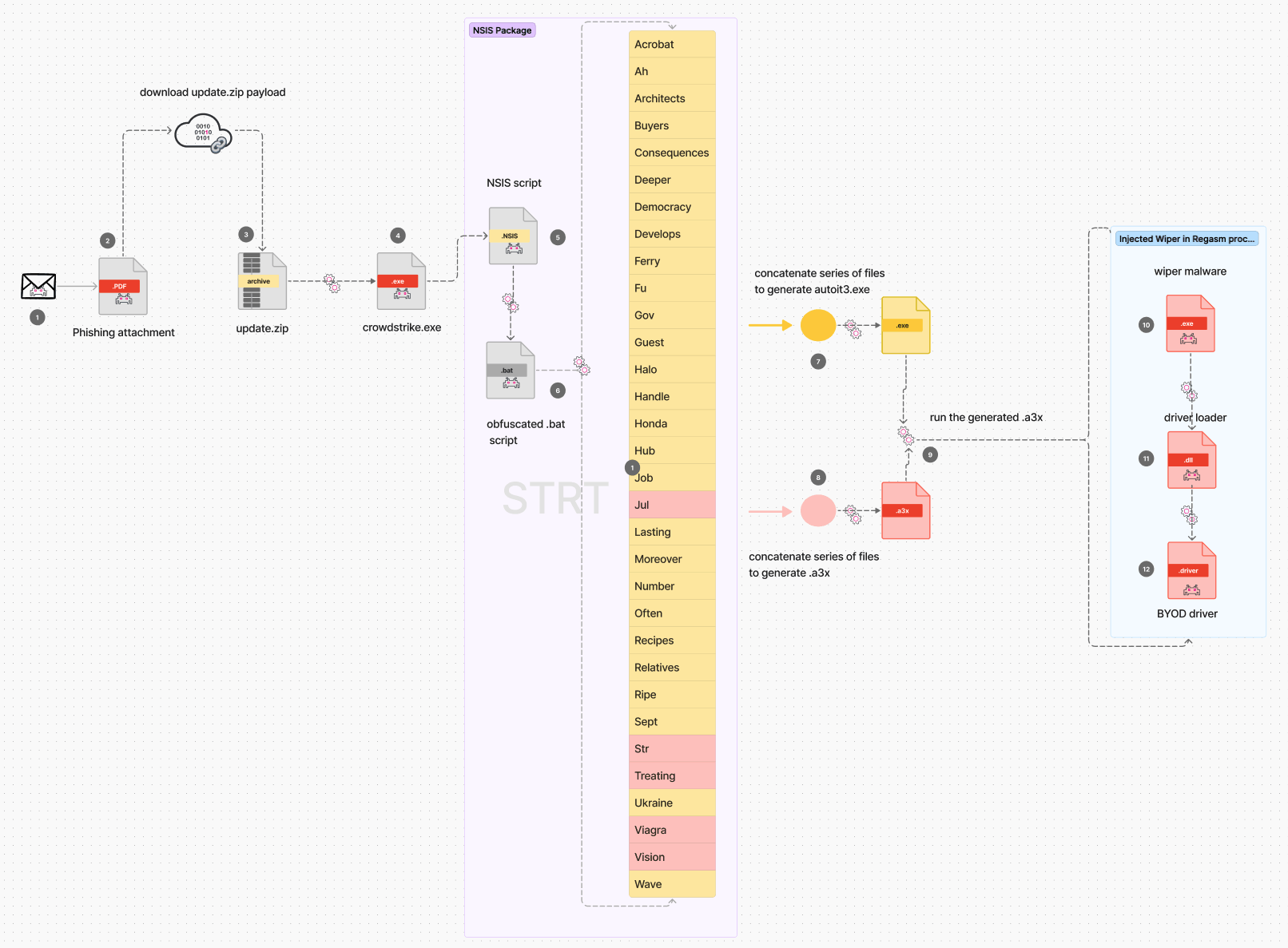
Attack chain of the July 2024 CrowdStrike-themed phishing campaign attributed to Handala, illustrating phishing delivery, NSIS-based payload staging, AutoIT loader execution, process hollowing into RegAsm.exe, and final wiper deployment with a BYOVD driver. (Source: Splunk)
| Technique Category | Description | Notable Tools / Examples |
| Wiper Arsenal | Handala’s operations rely heavily on destructive malware designed to overwrite files and render systems unusable. Several custom wipers have been documented across campaigns targeting both Windows and Linux environments. | BiBi Wiper, Hatef (.NET), Hamsa (Linux Bash), Cl Wiper (ElRawDisk driver), CoolWipe, ChillWipe, Handala Wiper |
| Initial Access & Social Engineering | The group frequently gains initial access through spear-phishing campaigns that exploit major events or public incidents to increase credibility. Victims are lured into downloading malicious archives disguised as legitimate tools or updates. | CrowdStrike outage phishing campaign (July 2024), spear-phishing emails and links |
| Multi-Stage Malware Execution | Handala campaigns typically use a staged execution chain designed to evade detection. Payload components are reconstructed at runtime and delivered through scripting frameworks before deploying the final wiper payload. | NSIS installer abuse, obfuscated batch scripts, AutoIT loaders, process hollowing into RegAsm.exe |
| Command-and-Control & Telemetry | Before triggering destructive routines, malware collects system information from compromised hosts and transmits it to operators through lightweight command channels. | Telegram Bot API used as C2 and telemetry channel |
| Additional Techniques | Several campaigns also employ privilege escalation and defense-evasion techniques to ensure successful payload execution. | BYOVD (ListOpenedFileDrv_32.sys), payload obfuscation, LOLBin abuse |
How Can Organizations Mitigate Handala Attacks?
- Phishing protection: Use phishing-resistant MFA and email filtering to block malicious attachments and links used for initial access.
- User awareness: Train employees to recognize phishing lures, especially those exploiting major events or technical incidents.
- Script monitoring: Detect abnormal execution of installers, batch scripts, and scripting tools such as AutoIT or PowerShell.
- LOLBin abuse detection: Monitor suspicious use of legitimate Windows utilities (e.g., RegAsm.exe) that may be abused for payload execution.
- Network monitoring: Inspect outbound connections and restrict unauthorized communication with messaging platforms used for C2 (e.g., Telegram APIs).
- Driver security controls: Enable vulnerable driver blocklists and prevent loading of unsigned or untrusted kernel drivers to mitigate BYOVD techniques.
- Endpoint protection: Deploy behavioral EDR detections for process hollowing, payload reconstruction, and destructive malware activity.
- Resilient backups: Maintain offline or immutable backups to enable recovery from destructive wiper attacks.
How Can SOCRadar Help?
Threat Actor Intelligence: SOCRadar provides continuous tracking of Handala and the broader MOIS ecosystem, including Scarred Manticore, MuddyWater, and affiliated personas. Campaign shifts, new wiper variants, and targeting changes are surfaced as they emerge.
Advanced Dark Web and Telegram Monitoring: SOCRadar monitors Handala’s Telegram channels, BreachForums account, TOR hidden services, and clearnet leak sites. Breach claims, doxxing activity, and “Saturday Files” releases are flagged in real time, giving security teams early warning before stolen data reaches wider circulation.
Attack Surface Management: Identifies exposed SharePoint instances, unpatched internet-facing applications, and misconfigured MDM platforms that Handala and its MOIS parent clusters target for initial access.
Iran-Israel Cyber Conflict Dashboard: SOCRadar’s dedicated conflict dashboard tracks the full spectrum of Iranian cyber activity, from state-sponsored APTs to hacktivist proxies like Handala. The dashboard provides analyst-vetted assessments rather than raw claims, separating verified intelligence from the noise of hundreds of daily Telegram posts.
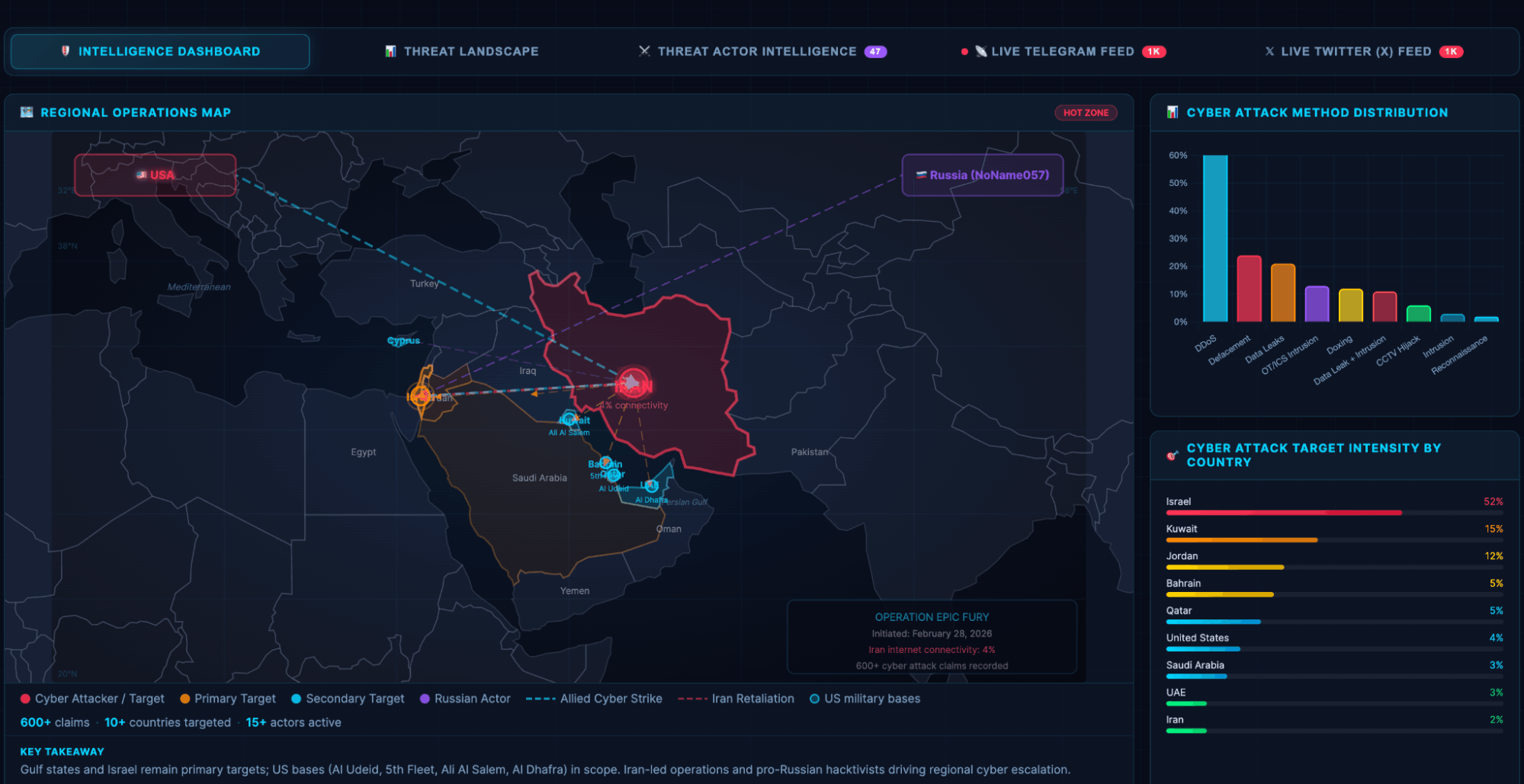
SOCRadar’s Iran-Israel Cyber Conflict Dashboard
What Are Handala’s MITRE ATT&CK TTPs?
| Tactic | Technique ID | Technique Name |
| Reconnaissance | T1589 | Gather Victim Identity Information |
| Reconnaissance | T1590 | Gather Victim Network Information |
| Initial Access | T1566.001 | Spear Phishing Attachment |
| Initial Access | T1566.002 | Spear Phishing Link |
| Initial Access | T1566.003 | Spear Phishing via SMS |
| Initial Access | T1078.004 | Valid Accounts: Cloud Accounts |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1059.010 | Command and Scripting Interpreter: AutoHotKey & AutoIT |
| Execution | T1204 | User Execution |
| Persistence | T1505.003 | Server Software Component: Web Shell |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1497.003 | Time-Based Evasion |
| Defense Evasion | T1055.012 | Process Hollowing |
| Defense Evasion | T1218 | System Binary Proxy Execution |
| Defense Evasion | T1090 | Proxy |
| Lateral Movement | T1021.001 | Remote Desktop Protocol |
| Exfiltration | T1020 | Automated Exfiltration |
| Impact | T1561.002 | Disk Structure Wipe |
| Impact | T1485 | Data Destruction |
| Impact | T1491 | Defacement |
If you would like a more detailed report on Handala’s Stryker Attack, including IoCs, YARA rules; contact info@socradar.io.
Article Link: https://socradar.io/blog/dark-web-profile-handala-hack/
1 post - 1 participant
Malware Analysis, News and Indicators - Latest topics